Every successful interview starts with knowing what to expect. In this blog, we’ll take you through the top Knowledge of Wireless Communications interview questions, breaking them down with expert tips to help you deliver impactful answers. Step into your next interview fully prepared and ready to succeed.
Questions Asked in Knowledge of Wireless Communications Interview
Q 1. Explain the difference between narrowband and wideband systems.
The key difference between narrowband and wideband systems lies in the bandwidth they utilize. Narrowband systems operate with a relatively small bandwidth, typically less than 200 kHz, while wideband systems employ a significantly larger bandwidth, often exceeding several MHz. Think of it like this: narrowband is like a thin water pipe carrying a small amount of data slowly, whereas wideband is a wide pipe that can carry much more data quickly.
Narrowband systems are better suited for applications where data rates are low and spectral efficiency isn’t the primary concern. Examples include older cellular systems or some low-power, long-range communication networks. Wideband systems, on the other hand, are crucial for high-speed data transmission, as seen in modern cellular networks (4G LTE, 5G), Wi-Fi, and other high-bandwidth applications. They can support significantly higher data rates but require more complex signal processing techniques.
Q 2. Describe various multiple access techniques like TDMA, FDMA, CDMA, OFDMA.
Multiple access techniques allow multiple users to share the same wireless channel. Several prominent methods exist:
- TDMA (Time Division Multiple Access): Users share the same frequency but are allocated different time slots. Imagine a highway with multiple lanes; each car (user) gets its own time slot to travel. This is relatively simple to implement but can be inefficient if some users are inactive.
- FDMA (Frequency Division Multiple Access): Users share the same time but are assigned different frequency bands. This is like dividing the highway into separate lanes – each lane (frequency) is used by a different car (user) simultaneously. FDMA is robust against interference but less spectrally efficient than some other methods.
- CDMA (Code Division Multiple Access): Users share the same time and frequency but are distinguished by unique codes. This is like all cars traveling on the same highway at the same time, but each car has a unique identification tag. CDMA is robust against interference but computationally complex.
- OFDMA (Orthogonal Frequency Division Multiple Access): A more advanced form of FDMA, OFDMA divides the available bandwidth into many smaller subcarriers, allowing flexible allocation of resources to different users. This is like having a highway with many lanes, each able to support different speeds and amounts of traffic based on demand. It’s highly efficient and used in 4G LTE and 5G.
Q 3. What are the advantages and disadvantages of MIMO technology?
MIMO (Multiple-Input Multiple-Output) technology utilizes multiple antennas at both the transmitter and receiver to enhance communication performance.
Advantages:
- Increased Data Rate: MIMO allows for the transmission of multiple data streams simultaneously, significantly boosting data rates.
- Improved Range and Reliability: Multiple antennas enable spatial diversity, mitigating fading and improving the link’s robustness.
- Enhanced Spectral Efficiency: MIMO allows for more efficient use of available bandwidth.
Disadvantages:
- Increased Complexity: MIMO systems are more complex than single-antenna systems, both in terms of hardware and signal processing.
- Higher Cost: The use of multiple antennas adds to the overall cost of the equipment.
- Calibration Challenges: Accurate calibration of multiple antennas is crucial for optimal performance.
MIMO is ubiquitous in modern wireless systems, including Wi-Fi and cellular networks, due to its significant performance benefits despite the added complexity and cost.
Q 4. Explain the concept of fading in wireless communication and mitigation techniques.
Fading in wireless communication refers to the fluctuation in signal strength caused by the propagation environment. Imagine shouting across a field – sometimes your voice is clear, and sometimes it’s weak due to obstacles or reflections. This variation in signal strength is fading.
Several types of fading exist, including Rayleigh fading (common in urban environments with many scatterers) and Rician fading (where a direct line-of-sight path exists along with scattered paths). Mitigation techniques include:
- Diversity Techniques: Employing multiple antennas or different frequencies to combine signals and reduce the impact of fading (discussed further in a later answer).
- Error Correction Coding: Adding redundancy to the transmitted data to enable recovery from errors induced by fading.
- Adaptive Modulation and Coding: Adjusting the modulation and coding schemes based on the channel conditions to optimize performance.
- Equalization: Compensating for the distortion introduced by the channel (discussed further in a later answer).
Q 5. Describe different types of wireless channel impairments.
Wireless channels are susceptible to various impairments that degrade signal quality:
- Path Loss: Signal strength decreases with distance from the transmitter.
- Shadowing: Obstacles like buildings and trees attenuate the signal.
- Multipath Propagation: Signals arrive at the receiver via multiple paths, causing constructive and destructive interference (leading to fading).
- Doppler Shift: Relative motion between the transmitter and receiver causes a frequency shift.
- Interference: Signals from other sources can interfere with the desired signal.
- Noise: Thermal noise and other forms of noise add to the signal, degrading its quality.
Q 6. How does equalization work in wireless communication?
Equalization is a signal processing technique used to compensate for the distortion introduced by the wireless channel. The channel’s multipath propagation and other impairments can alter the shape of the transmitted signal, causing intersymbol interference (ISI) – where the symbols overlap and become difficult to distinguish at the receiver.
Equalizers estimate the channel’s characteristics and apply an inverse filter to the received signal, effectively undoing the channel’s distortion. This improves the signal’s quality and enables reliable data recovery. Various equalization techniques exist, including linear equalization, decision feedback equalization, and minimum mean-square error (MMSE) equalization. The choice of equalization technique depends on the characteristics of the channel and the desired complexity.
Q 7. Explain the concept of diversity techniques in wireless systems.
Diversity techniques exploit the fact that independent signal copies (received via different paths or antennas) are less likely to fade simultaneously. This redundancy improves reliability and data rates.
Different types of diversity exist:
- Space Diversity: Using multiple antennas at the transmitter and/or receiver. Each antenna receives a slightly different signal, and these signals can be combined to mitigate fading.
- Frequency Diversity: Transmitting the same data on multiple frequencies. Fading affects different frequencies differently, so combining signals from multiple frequencies reduces the overall fading impact.
- Time Diversity: Transmitting the same data multiple times at different time instants. This works well if fading changes slowly over time.
- Polarization Diversity: Using antennas with different polarizations (e.g., vertical and horizontal). This helps because the fading characteristics of different polarizations may differ.
Diversity techniques are essential for reliable wireless communication, especially in challenging propagation environments.
Q 8. What are the key features of 5G technology compared to 4G?
5G represents a significant leap forward from 4G, offering dramatically increased speeds, lower latency, and greater capacity. Think of it like upgrading from a dial-up connection to fiber optics. Here’s a breakdown of the key differences:
- Peak Data Rates: 5G boasts peak data rates significantly higher than 4G, enabling faster downloads and uploads. This is crucial for applications like high-definition video streaming and augmented reality.
- Latency: 5G significantly reduces latency (the delay in data transmission), making it ideal for real-time applications like online gaming and autonomous driving. Imagine the difference between a laggy online game and one with instantaneous response.
- Capacity: 5G offers substantially increased network capacity, allowing more devices to connect simultaneously without performance degradation. This is vital in densely populated areas like city centers.
- Frequency Bands: 5G utilizes higher frequency bands (millimeter wave), offering wider bandwidth but with shorter range, complemented by lower-frequency bands for wider coverage. This allows for a combination of speed and reach.
- Network Architecture: 5G employs a more advanced network architecture, including network slicing and edge computing, enabling better resource management and improved performance for different applications.
In essence, 5G isn’t just a faster 4G; it’s a fundamentally different network designed for the demands of a hyper-connected world.
Q 9. Explain the difference between OFDM and OFDMA.
Both OFDM (Orthogonal Frequency-Division Multiplexing) and OFDMA (Orthogonal Frequency-Division Multiple Access) are digital modulation techniques used in wireless communication, but they differ in how they manage multiple users. Imagine OFDM as a highway with many lanes, all carrying data simultaneously, while OFDMA is like that same highway but with the added ability to assign lanes to specific vehicles (users).
- OFDM: Divides a wide frequency band into many smaller subcarriers, each carrying data. It’s efficient in combating multipath fading (signal distortion caused by reflections). Think of it as sending data in many small, independent packets, each more resistant to interference.
- OFDMA: An evolution of OFDM, it adds the capability of resource allocation across users. It allows for the dynamic allocation of subcarriers to different users based on their needs and channel conditions, making it more efficient and flexible in handling multiple users simultaneously. This is like a smart traffic management system on the highway, optimizing lane usage.
In summary, OFDMA is a more advanced version of OFDM, designed to optimize network capacity and efficiency in multi-user environments, leading to improved performance in 5G and beyond.
Q 10. Discuss different modulation techniques used in wireless communication.
Various modulation techniques are used in wireless communication to efficiently transmit data. The choice of modulation depends on factors like signal-to-noise ratio (SNR) and bandwidth requirements. Some common examples are:
- Amplitude Shift Keying (ASK): Represents data by changing the amplitude of the carrier signal. Simple but susceptible to noise.
- Frequency Shift Keying (FSK): Represents data by changing the frequency of the carrier signal. More robust to noise than ASK.
- Phase Shift Keying (PSK): Represents data by changing the phase of the carrier signal. Offers higher data rates than ASK and FSK.
- Quadrature Amplitude Modulation (QAM): Combines amplitude and phase shifting to achieve higher data rates. Commonly used in high-speed data applications like cable modems and DSL.
- Orthogonal Frequency-Division Multiplexing (OFDM): As discussed earlier, divides a wide frequency band into multiple subcarriers, each modulated independently, improving spectral efficiency.
Each modulation technique involves a trade-off between data rate, bandwidth usage, and robustness to noise and interference. The selection of the optimal technique is crucial for efficient and reliable wireless communication.
Q 11. What are the challenges in designing wireless sensor networks?
Designing wireless sensor networks (WSNs) presents unique challenges due to their resource-constrained nature and the often harsh environments in which they operate. Key challenges include:
- Energy Constraints: Sensors are typically battery-powered, requiring energy-efficient protocols and hardware.
- Limited Bandwidth: Wireless communication in WSNs often suffers from limited bandwidth, making efficient data transmission crucial.
- Scalability: Designing WSNs that can scale to hundreds or thousands of nodes presents a significant challenge.
- Reliability and Fault Tolerance: Nodes may fail due to environmental factors or battery depletion, requiring robust fault-tolerance mechanisms.
- Security: Protecting the data transmitted within the WSN from unauthorized access is vital.
- Data Aggregation and Routing: Efficiently gathering and routing data from numerous sensors to a central point poses a complex problem.
Overcoming these challenges requires careful consideration of hardware selection, protocol design, and network architecture. It’s a balancing act between functionality, energy efficiency, and cost.
Q 12. Explain the principles of beamforming in wireless systems.
Beamforming is a signal processing technique used to focus the transmitted signal in a specific direction, thereby increasing the signal strength in that direction and reducing interference in others. Imagine a spotlight versus a floodlight; beamforming is like focusing the spotlight onto a particular target.
It works by coordinating the phase and amplitude of signals transmitted from multiple antenna elements in an array. By carefully adjusting the phase shift of each antenna, the signals constructively interfere in the desired direction, creating a focused beam. This focused beam improves signal quality and reduces interference for the intended receiver.
Beamforming is widely used in applications like 5G cellular networks, Wi-Fi, and radar systems. It allows for improved data rates, reduced power consumption, and increased coverage efficiency.
Q 13. Describe various antenna types and their applications in wireless communication.
Various antenna types are used in wireless communication, each with specific characteristics and applications. Here are some common examples:
- Dipole Antenna: A simple, widely used antenna with a resonant frequency determined by its length. Often used in applications requiring omnidirectional coverage.
- Patch Antenna: A planar antenna etched onto a substrate, often used in mobile devices due to its compact size and ease of integration.
- Yagi-Uda Antenna: A directional antenna with high gain, commonly used in television reception and point-to-point communication.
- Microstrip Antenna: A compact, printed antenna suitable for integration into circuit boards, often found in handheld devices.
- Horn Antenna: A high-gain antenna providing a well-defined beam, used in applications like satellite communication and radar.
The choice of antenna type depends on factors such as required gain, radiation pattern, size constraints, and frequency band. For example, a high-gain antenna is suitable for long-distance communication, while a compact antenna is needed for mobile devices.
Q 14. How does power control work in a cellular network?
Power control in cellular networks is a crucial mechanism for managing interference, extending battery life, and improving overall network capacity. It involves dynamically adjusting the transmission power of mobile devices and base stations based on various factors.
Several techniques are used:
- Open-Loop Power Control: The mobile device adjusts its transmit power based on pre-defined parameters, such as the distance from the base station. It’s simple but less precise.
- Closed-Loop Power Control: The base station monitors the received signal strength from the mobile device and sends feedback to adjust the transmit power. This approach provides more accurate and dynamic power control.
The goal is to maintain a sufficient signal strength for reliable communication while minimizing interference to other users and extending battery life. Sophisticated algorithms are used to optimize power allocation across the network, ensuring fairness and efficiency.
Q 15. Explain the concept of handover in cellular networks.
Handover, also known as handoff, is a crucial process in cellular networks that ensures uninterrupted communication as a mobile device moves from one base station (cell tower) to another. Imagine you’re on a phone call and driving; your phone seamlessly switches between cell towers without dropping the call – that’s handover in action. It’s a seamless transition designed to maintain the connection quality and prevent service disruptions.
Several factors trigger a handover, including signal strength degradation, signal quality issues, load balancing within the network (to distribute users efficiently), and network optimization. The process involves complex algorithms that monitor signal strength, quality, and network conditions in neighboring cells. When a predetermined threshold is met, the network initiates a handover procedure to switch the connection to the cell offering the best signal quality and capacity. Different handover techniques exist, like hard handover (a complete break before connection to the new cell) and soft handover (a gradual transition, maintaining connection to multiple cells simultaneously for a smoother experience).
Types of Handover:
- Hard Handover: The connection to the old base station is broken before the connection to the new one is established. This can lead to brief interruptions.
- Soft Handover: The mobile station maintains connections to multiple base stations simultaneously. The connection is smoothly transferred to the best cell without interruption.
- Intra-frequency Handover: Handover happens within the same frequency band.
- Inter-frequency Handover: Handover occurs between different frequency bands. This is more complex but enables better spectrum utilization and can improve quality and coverage.
Effective handover management directly impacts user experience. Poor handover can result in dropped calls, data loss, and service disruptions. Cellular network operators invest heavily in optimizing handover strategies to ensure seamless connectivity.
Career Expert Tips:
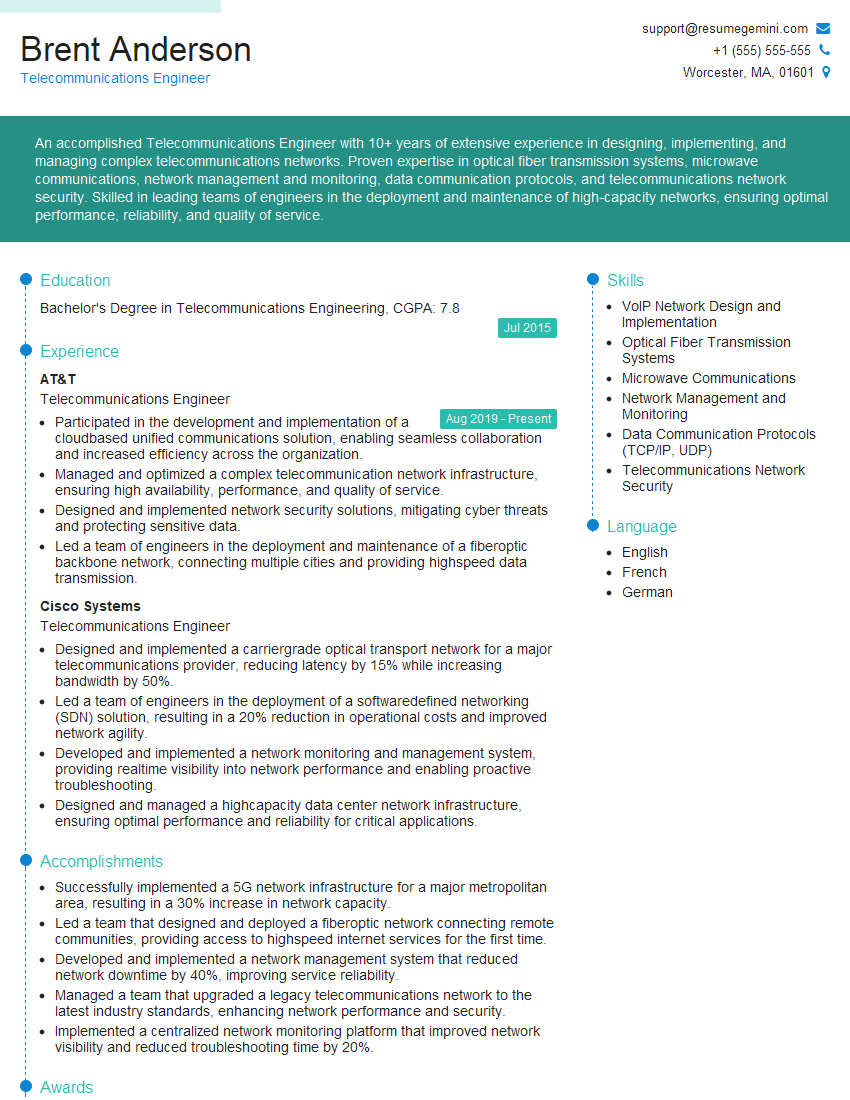
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe different types of error control codes.
Error control codes are crucial in wireless communication to ensure reliable data transmission despite the inherent noise and interference in the wireless medium. They add redundancy to the data, allowing the receiver to detect and correct errors introduced during transmission. Think of it as sending a message with extra clues to help the recipient understand it even if some parts are garbled.
There are two main categories:
- Block Codes: These operate on fixed-length blocks of data. They add extra bits (parity bits) to each block to detect or correct errors. Examples include Hamming codes and Reed-Muller codes. Hamming codes are commonly used for their simple implementation and ability to correct single-bit errors.
- Convolutional Codes: These codes operate on data streams continuously, encoding bits as they arrive. They offer better error correction capability than block codes for some situations. Viterbi decoding is a popular decoding algorithm for convolutional codes.
Examples of Error Control Techniques:
- Automatic Repeat Request (ARQ): The receiver requests retransmission of data blocks if errors are detected. This is a simple yet effective method for error control. There are different ARQ variants like Stop-and-Wait ARQ, Go-Back-N ARQ, and Selective Repeat ARQ, each with different trade-offs in efficiency and complexity.
- Forward Error Correction (FEC): The sender adds redundancy to the data, allowing the receiver to correct errors without retransmission. This is advantageous in situations where retransmission is impractical, such as satellite communication.
The choice of error control code depends on several factors, including the characteristics of the channel (noise level, bandwidth), the desired level of reliability, and the complexity of the encoder and decoder.
Q 17. What are the security considerations in wireless communication?
Security in wireless communication is paramount given the broadcast nature of the medium. Any data transmitted wirelessly is potentially vulnerable to interception, modification, or denial-of-service attacks. Protecting this data is critical.
Key security considerations include:
- Confidentiality: Ensuring that only authorized parties can access the transmitted data. This is often achieved using encryption techniques like AES (Advanced Encryption Standard).
- Integrity: Guaranteeing that the data has not been altered during transmission. Hashing algorithms (like SHA-256) and message authentication codes (MACs) are used to verify data integrity.
- Authentication: Verifying the identity of the communicating parties. This is typically done using protocols like EAP (Extensible Authentication Protocol) or digital certificates.
- Availability: Ensuring that the communication system is accessible to authorized users when needed. This involves protecting against denial-of-service (DoS) attacks and ensuring network robustness.
- Non-repudiation: Ensuring that the sender of a message cannot deny having sent it. Digital signatures are often employed for this purpose.
Security Protocols and Techniques: Wireless security protocols such as WPA2/3 (Wi-Fi Protected Access) for Wi-Fi networks and TLS/SSL (Transport Layer Security/Secure Sockets Layer) for secure web communication are commonly used to address these concerns. These protocols employ encryption, authentication, and integrity checks to protect wireless data transmissions.
The importance of robust security mechanisms cannot be overstated. Failure to adequately secure wireless communication can lead to serious consequences, including data breaches, financial losses, and reputational damage.
Q 18. Explain the concept of network slicing in 5G.
Network slicing in 5G is a revolutionary concept that allows mobile network operators to create multiple virtual networks (slices) on top of a single physical infrastructure. Imagine a pizza; the whole pizza is the physical network, but you can slice it into different sections (slices), each tailored to specific applications and service requirements.
Each slice is isolated and optimized for a particular use case, offering customized Quality of Service (QoS) parameters such as bandwidth, latency, and reliability. This enables the network to serve diverse applications with differing needs simultaneously, without compromising performance.
Examples of Network Slices:
- Enhanced Mobile Broadband (eMBB): A slice optimized for high-speed data applications, such as video streaming and high-definition content downloads.
- Ultra-Reliable Low Latency Communication (URLLC): A slice designed for applications requiring extremely low latency and high reliability, like autonomous driving and industrial automation.
- Massive Machine-Type Communication (mMTC): A slice optimized for the massive connectivity of IoT devices, prioritizing efficient communication with a large number of low-bandwidth devices.
Benefits of Network Slicing:
- Improved resource utilization: Efficient sharing of network resources.
- Enhanced service customization: Tailored QoS parameters for diverse applications.
- Increased flexibility and scalability: Efficient adaptation to changing network demands.
- New revenue opportunities: Offering specialized services to different market segments.
Network slicing is a key enabler for 5G’s vision of supporting a vast array of applications and services, offering a more efficient and versatile network infrastructure.
Q 19. Describe the different layers of the OSI model and their relevance to wireless communication.
The Open Systems Interconnection (OSI) model is a conceptual framework that divides network communication into seven distinct layers. Each layer has specific functions and protocols. While the OSI model is a reference model, real-world implementations might not always strictly adhere to all seven layers.
Layers and Relevance to Wireless Communication:
- Layer 1 (Physical): Deals with the physical transmission of bits over the medium. In wireless, this includes radio frequency (RF) transmission, antenna characteristics, modulation techniques, and signal power. Wireless standards like 802.11 (Wi-Fi) and cellular standards operate at this layer.
- Layer 2 (Data Link): Provides error-free transmission of data frames between two directly connected nodes. In wireless, MAC (Media Access Control) protocols like CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance) used in Wi-Fi manage access to the shared wireless medium. Frame formats and error detection mechanisms operate at this layer.
- Layer 3 (Network): Handles routing of packets between networks. In wireless, IP (Internet Protocol) addressing and routing protocols are crucial for connecting wireless devices to the internet. Mobile IP handles mobility in wireless networks.
- Layer 4 (Transport): Provides reliable and ordered data delivery. TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are common transport protocols. TCP ensures reliable delivery, while UDP is faster but less reliable.
- Layer 5 (Session): Manages connections between applications. Not as prominent in wireless compared to other layers.
- Layer 6 (Presentation): Deals with data formatting and presentation. Examples include data encryption and compression.
- Layer 7 (Application): The top layer involving applications like web browsers (HTTP), email (SMTP), and file transfer (FTP).
Understanding the OSI model is fundamental for anyone working in wireless communication, as it provides a framework for understanding how different aspects of the network interact to facilitate communication between wireless devices.
Q 20. How does location tracking work in wireless networks?
Location tracking in wireless networks uses various techniques to determine the geographical position of a device. The accuracy and methods employed vary greatly depending on the specific technology and application requirements.
Common Location Tracking Techniques:
- Cell ID Tracking: The simplest method uses the cell tower (base station) a device is connected to. It provides a coarse location, limited by the cell size (which can range from hundreds of meters to kilometers).
- Angle of Arrival (AoA): Multiple base stations measure the angle at which a signal arrives from the device. Trilateration or triangulation techniques are then used to pinpoint the location.
- Time of Arrival (ToA): Measures the time it takes for a signal to travel from the device to multiple base stations. The difference in arrival times is used to calculate the distance and determine the location.
- Time Difference of Arrival (TDoA): Similar to ToA, but uses the difference in arrival times between base stations to determine the location. This is more accurate than ToA.
- GPS (Global Positioning System): Devices equipped with a GPS receiver can determine their location by receiving signals from GPS satellites. This provides high accuracy but requires a clear line of sight to the satellites.
- Wi-Fi Positioning: Leverages Wi-Fi signal strength from multiple access points to estimate location. This is commonly used in indoor environments where GPS is often unavailable.
Challenges in Location Tracking: Accuracy can be affected by signal propagation, multipath fading (signals bouncing off objects), and environmental factors. Privacy concerns surrounding location data collection and its use are also significant considerations.
Q 21. What are the advantages and disadvantages of different spectrum allocation methods?
Spectrum allocation refers to how available radio frequencies are assigned for different uses. Efficient and effective allocation is crucial for optimal utilization of a scarce resource.
Common Spectrum Allocation Methods:
- Fixed Allocation: Specific frequency bands are permanently assigned to specific users or services. This provides stability and predictability but can lead to inefficient use of spectrum if assigned bands are underutilized.
- Dynamic Allocation: Frequency bands are assigned on demand, allowing more flexible and efficient use of the spectrum. Cognitive radio is a technology that enables dynamic spectrum access by intelligently identifying and utilizing underutilized spectrum.
- Auction-based Allocation: Frequency licenses are sold through auctions, allowing the market to determine the allocation based on economic efficiency. This can lead to higher revenue for regulators but may not always prioritize social needs.
- Command and Control Allocation: A central authority decides the allocation based on specific needs and priorities. This provides control but can be less efficient or flexible than market-based approaches.
Advantages and Disadvantages:
| Method | Advantages | Disadvantages |
|---|---|---|
| Fixed Allocation | Simplicity, Predictability | Inefficient use if underutilized |
| Dynamic Allocation | Efficient spectrum use, Flexibility | Complexity, potential interference |
| Auction-based Allocation | Efficient resource allocation (in theory), Revenue generation | Potential for market manipulation, may not prioritize social needs |
| Command and Control | Control over allocation, prioritization of needs | Lack of flexibility, potential inefficiency |
The best approach often depends on the specific context, technological capabilities, and regulatory environment. A combination of approaches might be employed to optimize spectrum utilization while addressing various societal and economic goals.
Q 22. Explain the concept of cognitive radio.
Cognitive radio is a revolutionary concept in wireless communication that allows wireless devices to intelligently sense their environment and adapt their transmission parameters to optimize spectrum usage. Imagine a radio that can ‘listen’ to the available frequencies and automatically choose the best one, avoiding interference and maximizing efficiency. This is fundamentally different from traditional radios which operate on pre-assigned frequencies.
Unlike traditional fixed-spectrum allocation, cognitive radios dynamically access available spectrum, making efficient use of underutilized frequencies. They achieve this through three key functions: spectrum sensing (detecting available channels), spectrum decision (choosing the best channel based on various parameters like signal strength, interference, and quality of service requirements), and spectrum management (adjusting transmission power and parameters to avoid interfering with primary users – those who are licensed to use the spectrum).
A practical example would be a smart device in a crowded Wi-Fi environment. A cognitive radio-enabled device could intelligently scan for the least congested channel, automatically switching to it and ensuring a better connection. This improves overall network capacity and user experience.
Q 23. Describe different protocols used in wireless communication (e.g., Zigbee, Bluetooth, Wi-Fi).
Wireless communication uses a variety of protocols, each designed for specific applications and requirements. Here are a few key examples:
- Wi-Fi (IEEE 802.11): This is the most common protocol for local area networking, offering high bandwidth for data transfer. It’s used extensively in homes, offices, and public hotspots. Different standards within 802.11 (like 802.11a/b/g/n/ac/ax) provide varying speeds and features.
- Bluetooth (IEEE 802.15.1): A short-range wireless technology ideal for connecting peripherals like keyboards, mice, and headsets. It prioritizes low power consumption and ease of use. Recent versions like Bluetooth 5 offer improved range and speed.
- Zigbee (IEEE 802.15.4): Designed for low-power, low-data-rate applications in sensor networks and home automation. It’s characterized by its mesh networking capability, allowing for robust and reliable communication even in challenging environments. Think smart home devices communicating with each other.
The choice of protocol depends on the specific application. For high-bandwidth data transfer, Wi-Fi is preferred; for short-range, low-power connections, Bluetooth is suitable; and for low-power sensor networks, Zigbee is a strong contender. The selection considers factors such as data rate, range, power consumption, and security requirements.
Q 24. What are the challenges related to deploying IoT devices on a large scale?
Deploying IoT devices at scale presents several challenges:
- Power management: Many IoT devices are battery-powered, requiring efficient energy management strategies to prolong their lifespan. This often involves sophisticated power saving modes and techniques.
- Security: The sheer number of interconnected devices creates a vast attack surface. Securing these devices against cyber threats is crucial, and requires robust authentication, encryption, and access control mechanisms.
- Scalability and interoperability: Managing and connecting millions of devices requires robust infrastructure and standardized protocols to ensure seamless communication and data exchange.
- Data management and analysis: The massive amount of data generated by IoT devices requires efficient storage, processing, and analysis capabilities. Big data technologies and cloud computing play a critical role here.
- Network congestion and interference: A high density of IoT devices can lead to network congestion and interference, requiring careful network planning and management.
Addressing these challenges requires a multi-faceted approach involving hardware optimization, secure software development, robust network infrastructure, and efficient data management techniques.
Q 25. Explain the impact of the Internet of Things (IoT) on wireless communication networks.
The Internet of Things (IoT) has significantly impacted wireless communication networks, leading to both opportunities and challenges. The massive growth in connected devices necessitates increased network capacity and improved efficiency.
Impact areas include:
- Increased network traffic: IoT devices generate vast amounts of data, placing a substantial burden on wireless networks. This necessitates development of efficient data compression and transmission techniques.
- Demand for low-power, wide-area networks (LPWANs): IoT applications often require long-range, low-power communication, driving the development and deployment of LPWAN technologies like LoRaWAN and Sigfox.
- Need for improved security: The proliferation of IoT devices increases the risk of security breaches, requiring robust security protocols and measures to protect against cyberattacks.
- Development of new communication protocols: Optimized protocols are being developed to handle the specific requirements of IoT devices, such as low power consumption and low latency.
- Edge computing: Processing data closer to the source (at the edge of the network) reduces latency and bandwidth consumption, which is essential for many real-time IoT applications.
In essence, IoT is driving innovation in wireless communication, pushing the boundaries of network capacity, efficiency, and security.
Q 26. Describe your experience with RF testing and measurement equipment.
My experience with RF testing and measurement equipment is extensive. I’m proficient in using various instruments, including spectrum analyzers, network analyzers, signal generators, power meters, and oscilloscopes. I’ve used these tools to perform a wide range of tests, such as:
- Signal strength and quality measurements: Assessing the strength and quality of wireless signals in different environments.
- Antenna characterization: Measuring antenna gain, impedance, and radiation patterns.
- Interference analysis: Identifying sources of interference and their impact on wireless communication.
- Compliance testing: Ensuring that devices meet regulatory standards (e.g., FCC, ETSI).
For example, I recently used a spectrum analyzer to identify the source of interference affecting a Wi-Fi network, which involved analyzing the frequency spectrum and pinpointing the interfering signal. This involved using the instrument’s sweep function and marker capabilities to analyze the frequency and power of signals. This ultimately allowed for corrective measures to be undertaken.
Q 27. How familiar are you with wireless network simulation tools?
I am very familiar with several wireless network simulation tools, including NS-3, MATLAB, and OPNET. I have used these tools extensively for various purposes such as:
- Network performance evaluation: Simulating network behavior under different conditions (e.g., varying traffic loads, node density) to assess performance metrics like throughput, delay, and packet loss.
- Protocol development and testing: Evaluating the performance and robustness of newly developed protocols in a simulated environment before deployment.
- Network planning and optimization: Designing and optimizing wireless networks by simulating various configurations to find the optimal solution for a given scenario. This often includes assessing the placement of base stations or access points.
I understand the importance of accurate modelling and validation, and I ensure that simulations are based on realistic parameters and scenarios.
Q 28. Describe your experience with wireless network optimization techniques.
My experience encompasses a range of wireless network optimization techniques. These techniques focus on enhancing network performance, capacity, and efficiency.
Some key techniques I’ve employed include:
- Channel planning and assignment: Optimizing channel selection to minimize interference and maximize capacity. This involves selecting channels with minimal overlap or interference from other sources, whether that’s other networks or other signals.
- Power control: Adjusting the transmission power of devices to improve signal quality and reduce interference. This is essential in reducing overall network noise.
- Antenna optimization: Selecting and positioning antennas to maximize coverage and minimize signal attenuation.
- Network topology design: Choosing the appropriate network architecture (e.g., star, mesh, tree) to meet specific requirements and optimize performance.
- Traffic management and QoS (Quality of Service): Implementing techniques to manage network traffic effectively and prioritize important data streams, ensuring quality of service for critical applications.
A recent project involved optimizing a cellular network’s coverage in a dense urban area. By carefully analyzing signal propagation patterns and using simulation tools, we identified optimal locations for deploying additional base stations, leading to a significant improvement in coverage and capacity.
Key Topics to Learn for Knowledge of Wireless Communications Interview
- Fundamental Concepts: Understanding modulation techniques (e.g., OFDM, QAM), channel models (e.g., Rayleigh, Rician fading), and multiple access schemes (e.g., TDMA, FDMA, CDMA, OFDMA).
- Wireless Standards: Deep dive into relevant standards like 5G NR, LTE, Wi-Fi (802.11ax/be), Bluetooth, and their architectures. Be prepared to discuss their strengths, weaknesses, and applications.
- Antenna Theory and Propagation: Grasp the basics of antenna characteristics (gain, directivity, polarization), path loss, and free-space propagation models. Understand concepts like MIMO and beamforming.
- Network Protocols: Familiarize yourself with network protocols relevant to wireless communication, including TCP/IP, routing protocols, and quality of service (QoS) mechanisms.
- Practical Applications: Be ready to discuss real-world applications of wireless technologies in areas like IoT, vehicular communication, and satellite communication. Consider case studies to illustrate your understanding.
- Signal Processing Techniques: Understand basic signal processing concepts such as filtering, equalization, and coding schemes used to mitigate noise and interference in wireless channels.
- Security in Wireless Networks: Discuss various security threats and countermeasures in wireless systems, including encryption algorithms, authentication protocols, and access control mechanisms.
- Problem-solving and Troubleshooting: Practice analyzing and resolving problems related to signal quality, network connectivity, and performance optimization in wireless networks. Develop your ability to explain your thought process clearly.
Next Steps
Mastering Knowledge of Wireless Communications opens doors to exciting and high-demand roles in a rapidly evolving industry. A strong understanding of these concepts will significantly enhance your interview performance and career prospects. To maximize your chances, create a compelling and ATS-friendly resume that highlights your skills and experience. ResumeGemini is a trusted resource that can help you build a professional resume tailored to your specific needs, ensuring your qualifications stand out. Examples of resumes tailored to Knowledge of Wireless Communications are available for your review, providing valuable guidance in showcasing your expertise effectively. Invest time in crafting a strong resume; it’s your first impression and a critical step in securing your dream job.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
To the interviewgemini.com Webmaster.
Very helpful and content specific questions to help prepare me for my interview!
Thank you
To the interviewgemini.com Webmaster.
This was kind of a unique content I found around the specialized skills. Very helpful questions and good detailed answers.
Very Helpful blog, thank you Interviewgemini team.