The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to Threat Assessment and Mitigation Planning interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in Threat Assessment and Mitigation Planning Interview
Q 1. Describe your experience in conducting threat assessments.
Conducting a threat assessment involves a systematic process of identifying, analyzing, and prioritizing potential threats to an organization’s assets. My experience spans various sectors, including finance, healthcare, and technology. I’ve led numerous assessments, employing both qualitative and quantitative methods. For example, in a recent engagement for a financial institution, I led a team in analyzing potential threats stemming from insider threats, phishing attacks, and denial-of-service attacks. This involved interviewing key personnel, reviewing security logs, and assessing existing security controls. The assessment resulted in a prioritized list of threats, enabling the client to focus resources effectively on the most critical vulnerabilities.
Another significant project involved assessing the cybersecurity posture of a healthcare provider. Here, the focus was on HIPAA compliance and the protection of patient data, which required a deep understanding of regulatory requirements and potential vulnerabilities related to data breaches. My approach always involves a careful balance of technical expertise and business context, ensuring that the assessment results are actionable and relevant to the client’s specific needs and operational realities.
Q 2. Explain the difference between qualitative and quantitative risk assessment.
Qualitative and quantitative risk assessments differ fundamentally in their approach to measuring risk. Qualitative assessment relies on subjective judgments and expert opinions to determine the likelihood and impact of threats. It uses descriptive scales (e.g., low, medium, high) to rate these factors. Think of it like a judgment call based on experience and available information. For instance, a qualitative assessment might conclude that a specific type of phishing attack is ‘highly likely’ to occur and have a ‘severe’ impact based on industry trends and expert knowledge.
Quantitative assessment, on the other hand, uses numerical data and statistical methods to measure risk. It aims to assign concrete values to the likelihood and impact of threats. This might involve analyzing historical data on security incidents or using probability models to estimate the likelihood of a specific threat. For example, a quantitative assessment might determine that a denial-of-service attack has a 20% probability of occurring within the next year and would result in a $500,000 loss.
In practice, a combined approach, using both qualitative and quantitative methods, often provides the most comprehensive understanding of risk. The qualitative assessment can help to identify potential threats that might be missed by quantitative methods alone, while the quantitative assessment provides a more precise and objective measurement of risk.
Q 3. What methodologies are you familiar with for threat modeling?
I’m proficient in several threat modeling methodologies, including STRIDE, PASTA, and DREAD.
- STRIDE (Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, Elevation of privilege) is a simple yet effective method for identifying potential threats to a system by categorizing them into six common threat types. It’s particularly useful for identifying potential security weaknesses in software applications.
- PASTA (Process for Attack Simulation and Threat Analysis) is a more structured and iterative approach. It focuses on modeling the system’s workflow and identifying potential attack paths. PASTA is especially valuable for complex systems where many components interact.
- DREAD (Damage potential, Reproducibility, Exploitability, Affected users, Discoverability) prioritizes threats based on their potential impact. This is crucial for focusing resources on the most critical vulnerabilities.
The choice of methodology depends heavily on the specific system being assessed and the available resources. For instance, STRIDE might be suitable for a small-scale project, whereas PASTA might be necessary for a larger, more complex system. My experience allows me to select and tailor the most appropriate methodology for each engagement.
Q 4. How do you prioritize threats and vulnerabilities?
Threat and vulnerability prioritization is critical for effective risk management. I typically employ a risk matrix, combining the likelihood and impact of each threat and vulnerability. This matrix allows for a visual representation of risks, enabling efficient prioritization.
Factors considered in the prioritization process include:
- Likelihood: How likely is the threat to occur?
- Impact: What would be the consequences if the threat materialized?
- Vulnerability Severity: How easily can the vulnerability be exploited?
- Business Criticality: How critical is the affected asset to the organization’s operations?
- Cost of Mitigation: How much would it cost to address the vulnerability?
After assigning numerical scores (or using qualitative assessments) based on these criteria, I use a risk matrix to visually prioritize threats and vulnerabilities. Those with the highest risk scores (high likelihood and high impact) receive the highest priority and require immediate attention. This ensures that resources are allocated to address the most critical risks first.
Q 5. What are the key components of a comprehensive mitigation plan?
A comprehensive mitigation plan should include several key components:
- Risk Assessment Summary: A concise overview of the identified threats and vulnerabilities and their associated risks.
- Mitigation Strategies: Detailed plans for addressing each identified risk, including specific actions, responsibilities, and timelines. Examples include implementing security controls, patching vulnerabilities, and conducting security awareness training.
- Resource Allocation: A clear outline of the budget, personnel, and other resources required to implement the mitigation strategies.
- Implementation Plan: A step-by-step plan outlining how the mitigation strategies will be implemented, including timelines, milestones, and responsibilities.
- Testing and Validation: A plan for testing the effectiveness of the implemented mitigation strategies to verify their efficacy.
- Monitoring and Review: A plan for ongoing monitoring and review of the mitigation strategies to ensure their continued effectiveness. This may include regular vulnerability scans, security audits, and penetration testing.
- Incident Response Plan: A plan outlining the procedures to follow in the event of a security incident.
The plan should be documented clearly and concisely, making it easily accessible and understandable to all relevant stakeholders. Regular review and updates are vital to ensure the plan remains relevant and effective in the ever-changing threat landscape.
Q 6. Explain your experience with vulnerability management.
My experience in vulnerability management encompasses the entire lifecycle, from vulnerability identification to remediation. I’m skilled in using various vulnerability scanning tools to identify weaknesses in systems and applications. I’ve worked with tools such as Nessus, OpenVAS, and QualysGuard, employing automated and manual methods to gain a comprehensive understanding of the organization’s vulnerability landscape.
Beyond identifying vulnerabilities, my expertise extends to the crucial aspects of vulnerability prioritization, remediation, and verification. I’ve developed and implemented processes for efficiently managing vulnerabilities, ensuring that critical vulnerabilities are addressed promptly and effectively. I emphasize a risk-based approach, prioritizing remediation efforts based on factors such as the severity of the vulnerability, its exploitability, and the impact of a successful exploit. My experience includes collaborating with development teams to address vulnerabilities within applications, working closely with system administrators to patch vulnerabilities in operating systems, and implementing security controls to mitigate risks where patching isn’t feasible.
Regular reporting and communication are essential aspects of effective vulnerability management. I consistently provide clear and concise reports to stakeholders, updating them on the status of identified vulnerabilities and the progress of remediation efforts. This proactive communication promotes transparency and accountability, ensuring that everyone understands the organization’s security posture and the steps being taken to improve it. Furthermore, I have experience with developing and implementing vulnerability management processes that align with relevant compliance frameworks, such as ISO 27001 and NIST Cybersecurity Framework.
Q 7. Describe your understanding of the NIST Cybersecurity Framework.
The NIST Cybersecurity Framework (CSF) is a voluntary framework that provides a set of standards, guidelines, and best practices to manage and reduce cybersecurity risk. It’s a flexible and adaptable framework that can be tailored to organizations of all sizes and across various sectors. I understand the five core functions of the CSF: Identify, Protect, Detect, Respond, and Recover.
- Identify: This involves identifying assets, systems, and data that need protection.
- Protect: This involves developing and implementing safeguards to limit or contain the impact of a cybersecurity event.
- Detect: This involves developing and implementing ways to identify the occurrence of a cybersecurity event.
- Respond: This involves developing and implementing a plan to take action regarding a detected cybersecurity event.
- Recover: This involves developing and implementing a plan to restore any capabilities or services that were impaired due to a cybersecurity event.
My experience in utilizing the NIST CSF involves aligning organizational security practices with the framework’s tiers, which represent the increasing maturity and sophistication of an organization’s cybersecurity capabilities. I have successfully helped organizations assess their current cybersecurity posture against the NIST CSF, identify gaps, and develop improvement plans. Furthermore, I’ve used the framework to guide the development of security policies and procedures, ensuring alignment with best practices and regulatory requirements.
Q 8. How do you incorporate threat intelligence into your risk assessments?
Threat intelligence is crucial for accurate risk assessments. I incorporate it by actively consuming feeds from various sources – commercial threat intelligence platforms, open-source intelligence (OSINT) resources like vulnerability databases (e.g., CVE), and government advisories. This intelligence informs the likelihood and impact assessments within my risk matrix. For instance, if a vulnerability is reported affecting a specific software we use (say, a widely used CRM), and threat intelligence indicates active exploitation attempts, I significantly increase the likelihood score of that risk in my assessment. This allows us to prioritize resources effectively towards mitigating the most pressing threats.
Specifically, I use a structured process: First, I identify our assets and their vulnerabilities. Then, I cross-reference this with threat intelligence to determine if these vulnerabilities are actively being targeted. Finally, I assess the potential impact of a successful attack, leading to a prioritized list of risks that can be presented to stakeholders.
Q 9. How do you communicate risk effectively to both technical and non-technical audiences?
Communicating risk effectively requires tailoring the message to the audience. For technical audiences, I use precise terminology and detailed technical reports outlining vulnerabilities, attack vectors, and proposed solutions. For non-technical audiences, I use simple language, analogies, and visualizations (charts, graphs) to convey the potential impact of risks in business terms – financial losses, reputational damage, or operational disruptions. For example, instead of saying “SQL injection vulnerability,” I might say, “Imagine someone breaking into our customer database and stealing sensitive information.” This approach ensures everyone understands the stakes and the importance of mitigation.
A common approach is using a simple risk matrix that visualizes likelihood and impact. I might also employ storytelling, presenting scenarios of potential attacks and their consequences to resonate emotionally with the audience and motivate action.
Q 10. Describe a time you identified a critical threat and implemented mitigation strategies.
In a previous role, we identified a critical vulnerability in our web application allowing for unauthorized access to sensitive customer data. Threat intelligence indicated similar vulnerabilities were being actively exploited in the wild. We immediately followed incident response procedures. Our mitigation strategy involved a multi-pronged approach:
- Immediate Patching: We deployed an emergency patch to address the vulnerability.
- Intrusion Detection System (IDS) Enhancement: We enhanced our IDS rules to detect and alert on similar attack patterns.
- Vulnerability Scanning: We conducted a thorough vulnerability scan to identify any other potential weaknesses.
- Security Awareness Training: We provided additional security awareness training to our employees on phishing and social engineering.
- Incident Response Plan Rehearsal: We conducted a table-top exercise to practice our response capabilities.
The swift response prevented a data breach, protecting customer information and the company’s reputation. This highlighted the importance of proactive threat monitoring and rapid incident response capabilities.
Q 11. What are your preferred tools for threat assessment and mitigation?
My preferred tools depend on the specific needs of the assessment, but generally include:
- Vulnerability Scanners: OpenVAS, Nessus, QualysGuard for identifying vulnerabilities in systems and applications.
- Security Information and Event Management (SIEM) systems: Splunk, QRadar for collecting and analyzing security logs to detect suspicious activities.
- Threat Intelligence Platforms: Recorded Future, ThreatQuotient for accessing and analyzing threat feeds.
- Risk Management Software: Various platforms assist in building and tracking risk assessments and mitigation plans.
I also utilize scripting languages like Python for automation tasks such as vulnerability scanning and data analysis. The choice of tools is always guided by the context of the assessment, budget, and the organization’s existing infrastructure.
Q 12. How do you stay current with emerging threats and vulnerabilities?
Staying current is paramount. I leverage several strategies:
- Subscription to threat intelligence feeds: This includes commercial platforms and free open-source resources.
- Industry conferences and webinars: Attending events keeps me updated on emerging threats and best practices.
- Following security researchers and experts on social media and blogs: This provides insights into cutting-edge research and real-world threat analysis.
- Regularly reviewing industry publications and research papers: This allows me to stay abreast of the latest trends and advancements in threat assessment and mitigation.
- Participating in online security communities: Forums and communities offer opportunities for discussion and knowledge exchange.
Continuous learning is critical in this rapidly evolving field.
Q 13. Explain your experience with incident response planning and execution.
My experience with incident response planning and execution is extensive. I’ve been involved in developing and implementing incident response plans for various organizations, aligning them with frameworks like NIST Cybersecurity Framework. This includes defining roles and responsibilities, establishing communication protocols, outlining procedures for containment, eradication, recovery, and post-incident activity.
During incident response, I follow a structured methodology, starting with initial triage and investigation, containment and eradication of the threat, recovery of affected systems, and post-incident analysis to improve future preparedness. A successful response requires coordination across different teams, clear communication, and a calm, methodical approach. I’ve also conducted numerous tabletop exercises to prepare teams for real-world incidents and ensure the plan remains relevant and functional.
Q 14. How do you measure the effectiveness of your mitigation strategies?
Measuring the effectiveness of mitigation strategies is crucial. I use several methods:
- Key Risk Indicators (KRIs): Monitoring metrics like the number of successful phishing attempts, detected vulnerabilities, or security incidents helps assess the impact of our mitigation efforts.
- Vulnerability scanning results: Tracking the reduction in the number of identified vulnerabilities over time indicates the effectiveness of patching and remediation efforts.
- Security awareness training results: Measuring employee knowledge through quizzes and simulated phishing campaigns helps assess the success of training programs.
- Post-incident analysis: After an incident, a thorough analysis identifies weaknesses and improvements needed in our mitigation strategy.
- Return on Security Investment (ROSI): Evaluating the cost of implementing mitigation strategies against the potential financial losses avoided helps justify security investments.
Regularly reviewing and adjusting our mitigation strategies based on performance data ensures we are effectively managing and reducing our risks.
Q 15. What is your approach to managing risk in a dynamic environment?
Managing risk in a dynamic environment requires a proactive and adaptable approach. It’s not about eliminating all risk – that’s impossible – but about understanding, prioritizing, and mitigating the most significant threats. My approach centers around a continuous risk assessment process, leveraging a combination of qualitative and quantitative methods.
- Continuous Monitoring: I utilize automated tools and dashboards to monitor emerging threats and vulnerabilities in real-time. This allows for quick identification of changes in the threat landscape and immediate adjustments to our mitigation strategies. For example, if a new zero-day exploit emerges, we can immediately assess its potential impact and implement temporary countermeasures.
- Scenario Planning: I regularly conduct tabletop exercises and simulations to test our response to various high-impact threats. This helps identify gaps in our preparedness and refine our incident response plans. A recent exercise simulating a ransomware attack allowed us to identify a weakness in our data backup procedures, leading to immediate improvements.
- Prioritization: I use a risk matrix that combines the likelihood and impact of potential threats to prioritize mitigation efforts. This ensures we focus on the most critical vulnerabilities first. Resources are not infinite, so this is a crucial step.
- Adaptive Response: Our mitigation strategies are not static. They are regularly reviewed and updated based on the results of our continuous monitoring, scenario planning, and risk assessments. The dynamic nature of threats mandates this agility.
Essentially, it’s a cyclical process of assess, prioritize, mitigate, monitor, and adapt – constantly refining our approach to stay ahead of evolving threats.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe your experience with regulatory compliance (e.g., HIPAA, GDPR).
I have extensive experience with regulatory compliance, particularly HIPAA and GDPR. My approach involves a multi-faceted strategy that includes:
- Comprehensive Risk Assessment: I conduct thorough assessments to identify areas of vulnerability related to protected health information (PHI) under HIPAA and personal data under GDPR. This often involves data mapping exercises to pinpoint exactly where sensitive data resides.
- Policy Development and Implementation: I work with stakeholders to develop and implement robust policies and procedures that align with regulatory requirements. This includes data security policies, access control policies, incident response plans, and employee training programs.
- Technical Safeguards: I’m proficient in implementing technical controls such as encryption, access controls, and intrusion detection systems to protect sensitive data. This includes regular security audits to verify compliance.
- Auditing and Monitoring: Regular audits and ongoing monitoring are crucial to ensure continuous compliance. This involves reviewing access logs, security alerts, and conducting periodic penetration testing.
- Employee Training: I develop and deliver training programs for employees to educate them on data privacy regulations and security best practices. This reduces the risk of human error, a major cause of data breaches.
For example, in a previous role, I successfully guided the organization through a HIPAA audit, addressing all findings and demonstrating our compliance with the regulations. This involved not only technical fixes but also procedural changes and improved employee training.
Q 17. How do you handle conflicting priorities in threat mitigation?
Conflicting priorities in threat mitigation are inevitable. My approach to handling them involves a structured process of:
- Prioritization Framework: I use a risk-based prioritization framework, considering the likelihood and impact of each threat. This ensures that resources are allocated to the most critical vulnerabilities first.
- Stakeholder Collaboration: I engage with stakeholders to understand their concerns and priorities, facilitating open communication and compromise. This might involve explaining the tradeoffs of different mitigation options.
- Data-Driven Decision-Making: I use data analytics to inform my decisions, presenting clear evidence of the risks and potential impacts of different choices. This approach provides a more objective basis for resolving conflicts.
- Phased Approach: Sometimes, complete mitigation of all threats isn’t immediately feasible. In such cases, I recommend a phased approach, addressing the most critical issues first and then tackling others as resources permit.
- Documentation and Reporting: Clear documentation of decisions, including justifications and trade-offs, is crucial for transparency and accountability. This also facilitates future decision-making.
For instance, if a budget constraint prevents simultaneous implementation of all recommended security controls, I’d prioritize those that protect the most critical assets and data, perhaps using a phased rollout for less critical systems.
Q 18. What is your experience with developing and maintaining security policies and procedures?
I have extensive experience in developing and maintaining security policies and procedures. My approach focuses on creating comprehensive, understandable, and enforceable documents that align with organizational goals and regulatory requirements.
- Needs Assessment: I begin by conducting a thorough needs assessment to understand the organization’s specific security risks and regulatory obligations. This helps to tailor the policies to the organization’s context.
- Policy Development: I develop clear, concise, and actionable security policies that cover various aspects of information security, such as access control, data protection, incident response, and acceptable use.
- Stakeholder Engagement: I actively involve stakeholders in the policy development process, ensuring that policies are aligned with their needs and responsibilities. This process is vital for buy-in and effective implementation.
- Implementation and Training: I work with stakeholders to implement the policies and provide comprehensive training to employees on the new procedures. This includes regular refresher courses to keep knowledge up-to-date.
- Monitoring and Review: I regularly monitor the effectiveness of the policies and procedures and review them at least annually, making updates as needed to reflect changes in the threat landscape or organizational priorities. This ensures policies remain relevant.
I use a version control system to manage changes to the policies and procedures, ensuring that everyone has access to the most up-to-date versions. This transparent approach fosters compliance and reduces the chance of error.
Q 19. How do you use data analytics to support threat assessment and mitigation?
Data analytics is essential for effective threat assessment and mitigation. I utilize various techniques to gain actionable insights from security data:
- Log Analysis: I analyze security logs from various sources – firewalls, intrusion detection systems, and application servers – to identify patterns and anomalies that indicate potential threats. This helps identify unusual activity that might signal an attack.
- Threat Intelligence: I integrate threat intelligence feeds into our analysis to identify emerging threats and vulnerabilities that could affect our organization. This proactive approach allows us to stay ahead of the curve.
- Vulnerability Management: I use data analytics to prioritize vulnerability remediation efforts, focusing on the most critical vulnerabilities first. This involves correlating vulnerability data with asset criticality.
- Security Information and Event Management (SIEM): I leverage SIEM systems to collect, correlate, and analyze security data from multiple sources, providing a holistic view of the organization’s security posture. SIEM systems can automate alerts on suspicious activity.
- Machine Learning: In some cases, I use machine learning algorithms to detect anomalies and predict potential threats. This enhances our ability to identify threats that might go unnoticed using traditional methods.
For example, by analyzing log data, we recently identified a pattern of unauthorized access attempts from a specific IP address, which led to the immediate blocking of that IP and a subsequent investigation that prevented a potential breach.
Q 20. Explain your understanding of different types of threats (e.g., internal, external, cyber).
Understanding different types of threats is crucial for effective threat assessment and mitigation. Threats can be categorized in many ways, but some common types include:
- Internal Threats: These threats originate from within the organization, such as malicious or negligent employees, contractors, or insiders. Examples include data theft, sabotage, and accidental data breaches.
- External Threats: These threats originate from outside the organization, such as cyberattacks, physical theft, natural disasters, and espionage. This includes malware, phishing attacks, and DDoS attacks.
- Cyber Threats: These threats leverage technology to compromise systems and data. This is a broad category including malware, phishing, ransomware, denial-of-service attacks, and SQL injection.
- Physical Threats: These threats involve physical access to organizational assets, such as theft, vandalism, or unauthorized entry to facilities. Proper physical security measures are vital to mitigate these threats.
- Natural Threats: These threats are caused by natural events, such as fires, floods, earthquakes, and hurricanes. Business continuity and disaster recovery plans are essential to mitigate their impact.
Understanding the source and nature of each threat type is key to developing effective mitigation strategies. For example, mitigating internal threats might involve employee background checks, access control restrictions, and security awareness training, while mitigating cyber threats requires robust security infrastructure and incident response planning.
Q 21. What is your approach to conducting a post-incident review?
A post-incident review is critical for learning from past events and improving future preparedness. My approach to conducting a post-incident review is systematic and comprehensive:
- Fact-Finding: The first step involves gathering all relevant information about the incident, including logs, reports, and interviews with affected individuals. This step strives for objective fact-finding, not blame assignment.
- Timeline Reconstruction: I create a detailed timeline of the incident to understand the sequence of events. This helps to identify critical points and areas for improvement.
- Root Cause Analysis: I conduct a thorough root cause analysis to identify the underlying causes of the incident. This often involves using techniques like the ‘5 Whys’ to delve deep into the causes of the problem.
- Lessons Learned: Based on the root cause analysis, I identify lessons learned and recommend specific improvements to security policies, procedures, and technologies. This is a crucial stage for prevention of similar incidents in future.
- Documentation and Communication: I document all findings and recommendations in a detailed report, which is then communicated to relevant stakeholders. This ensures that the lessons learned are disseminated effectively.
- Implementation and Follow-up: I work with stakeholders to implement the recommended improvements and follow up to ensure that they are effective. This verification ensures that the review wasn’t just an exercise.
The goal of a post-incident review is not to assign blame but to learn from mistakes and strengthen our security posture. I emphasize a culture of continuous improvement, where incidents are treated as learning opportunities rather than failures.
Q 22. Describe your experience working with security information and event management (SIEM) systems.
My experience with Security Information and Event Management (SIEM) systems is extensive. SIEMs are the central nervous system of a robust security posture, aggregating logs and events from various sources to provide a unified view of an organization’s security landscape. I’ve worked with several leading SIEM platforms, including Splunk, QRadar, and Azure Sentinel, deploying, configuring, and optimizing them for different organizational needs.
In my previous role, I was instrumental in implementing a Splunk instance for a large financial institution. This involved not only the technical setup but also the development of custom dashboards and alerts tailored to detect specific threats relevant to their industry. For example, we created a dashboard that visualized real-time login attempts, highlighting unusual login locations or patterns. This allowed us to quickly identify and investigate potential brute-force attacks. I also developed alerts that triggered investigations when suspicious file transfers were detected, helping us prevent data breaches. Beyond implementation, my expertise extends to correlating data from various sources to identify sophisticated attacks that might otherwise go undetected by individual security tools.
Furthermore, I’m proficient in using SIEM data for threat hunting and incident response. I regularly utilize SIEM capabilities like threat intelligence integration and anomaly detection to proactively identify potential threats and to rapidly respond to security incidents. This includes developing and refining search queries and creating custom reports to analyze security trends and improve our organization’s overall security posture.
Q 23. How do you ensure your threat assessments and mitigation plans are cost-effective?
Cost-effectiveness in threat assessment and mitigation is paramount. It’s not just about finding the cheapest solution; it’s about maximizing the return on security investment (ROSI). I achieve this through a multi-pronged approach:
- Prioritization based on risk: I use a risk assessment framework (like NIST’s risk management framework) to identify and prioritize threats based on their likelihood and potential impact. This ensures resources are focused on the most critical vulnerabilities.
- Cost-benefit analysis: For each mitigation strategy, I conduct a thorough cost-benefit analysis, weighing the cost of implementation against the potential reduction in risk. This allows for informed decision-making, ensuring we only invest in solutions with a justifiable ROI.
- Leveraging free and open-source tools: Whenever feasible, I leverage free and open-source security tools (like OSSEC, Fail2ban, or Wireshark) to supplement commercial solutions, reducing overall costs without compromising security.
- Automation: Automating security tasks, such as vulnerability scanning and patch management, significantly reduces operational costs and frees up security personnel to focus on more strategic initiatives.
- Proactive security measures: Focusing on proactive security measures, like security awareness training and robust security architecture design, can significantly reduce the likelihood of incidents, ultimately saving costs associated with incident response.
For instance, instead of deploying a costly, enterprise-grade intrusion detection system for a small business, I might recommend a combination of open-source tools and carefully configured firewall rules, effectively addressing the most critical threats within a limited budget.
Q 24. How do you handle situations where resources are limited for mitigation?
Limited resources necessitate a strategic and prioritized approach. When resources are constrained, I employ the following strategies:
- Prioritization: I rigorously prioritize threats based on their likelihood and impact, focusing on mitigating the highest-risk vulnerabilities first. This involves creating a risk matrix to visualize and communicate the prioritization.
- Phased approach: Instead of attempting a complete solution immediately, I recommend a phased approach where mitigation efforts are implemented gradually, starting with the most critical issues. This allows for better resource allocation and avoids overwhelming the team.
- Collaboration and education: I encourage collaboration across different departments to share security responsibility and leverage existing resources. Security awareness training for all staff is also vital in mitigating human error, a common source of vulnerabilities.
- Leveraging existing infrastructure: I assess the existing security infrastructure to determine if there are underutilized resources that can be re-purposed for threat mitigation, avoiding unnecessary expenditures.
- Seeking external partnerships: In some cases, partnering with external organizations, or utilizing cloud-based security services, can be more cost-effective than investing in costly internal infrastructure.
For example, if a budget doesn’t allow for a new firewall, we may enhance existing firewall rules, conduct more frequent vulnerability scans, and implement stronger access controls to mitigate the risk.
Q 25. Explain your experience with penetration testing and ethical hacking.
My experience in penetration testing and ethical hacking is extensive. I’ve led numerous penetration testing engagements, employing both black-box and white-box testing methodologies to identify vulnerabilities in systems and applications. My expertise spans various areas, including network security assessments, web application penetration testing, and mobile application security testing. I’m proficient in using various tools and techniques, adhering strictly to ethical guidelines and legal boundaries.
For example, during a recent penetration test for a client, I identified a critical SQL injection vulnerability in their web application. This vulnerability could have allowed an attacker to access sensitive customer data. I documented the vulnerability with detailed steps on how to exploit it, as well as recommendations for remediation, such as input validation and parameterized queries. Beyond identifying vulnerabilities, I also provide clients with comprehensive reports containing detailed findings, remediation recommendations, and prioritized vulnerability ratings. This allows them to effectively address the identified weaknesses and improve their overall security posture.
Ethical hacking is not just about finding vulnerabilities; it’s about understanding the attacker’s mindset and leveraging that knowledge to strengthen security. My experience includes working with various open-source penetration testing tools such as Metasploit, Nmap, and Burp Suite, as well as commercial tools like Nessus and QualysGuard. This broad skillset allows me to tailor my approach to different client needs and security landscapes.
Q 26. How do you balance security with operational efficiency?
Balancing security and operational efficiency is a crucial aspect of my work. It’s about finding the sweet spot where security doesn’t hinder productivity and operational efficiency doesn’t compromise security. This balance is achieved through several strategies:
- Automation: Automating security tasks, such as vulnerability scanning, patch management, and user provisioning, frees up IT staff to focus on other critical tasks without sacrificing security.
- Integration: Integrating security tools with existing IT infrastructure minimizes disruption and maximizes efficiency. This includes seamless integration with existing monitoring systems and workflows.
- User-friendly security policies: Implementing clear, concise, and user-friendly security policies minimizes friction for employees and increases compliance. Complicated policies often lead to frustration and workarounds, weakening security.
- Continuous improvement: Regularly reviewing and updating security policies and procedures ensures they remain effective and efficient, adapting to evolving threats and organizational changes.
- Risk-based approach: Implementing a risk-based approach ensures resources are focused on the areas that pose the most significant risk, without overspending on less critical aspects.
For instance, instead of implementing a highly restrictive security policy that hinders productivity, I might implement a multi-factor authentication system, a more user-friendly approach that enhances security without disrupting workflow.
Q 27. Describe a situation where you had to make a difficult decision regarding risk.
In a previous role, we discovered a critical vulnerability in a legacy system that was essential for daily operations. Patching the vulnerability would require significant downtime, potentially impacting revenue and customer satisfaction. The alternative was to leave the vulnerability unpatched, increasing the risk of a security breach with potentially severe consequences. This presented a difficult risk-based decision.
To address this, I assembled a team comprising technical experts, business stakeholders, and legal representatives. We systematically assessed the risks and benefits of each approach, considering factors such as the likelihood and impact of a breach, the cost of downtime, and potential legal liabilities. We developed a risk matrix to visualize the trade-offs and debated the pros and cons of each option. We then proposed a mitigation plan that involved a phased rollout of a patch, coupled with increased monitoring and intrusion detection measures. This allowed us to minimize downtime while significantly reducing the risk of a breach. The team worked diligently to execute the plan with minimal disruption, ultimately ensuring both operational continuity and improved security.
This experience underscored the importance of careful risk assessment, collaborative decision-making, and the development of well-defined mitigation strategies in resolving complex security challenges.
Key Topics to Learn for Threat Assessment and Mitigation Planning Interview
- Threat Identification and Analysis: Understanding various threat vectors (cyber, physical, human), employing intelligence gathering techniques, and utilizing threat modeling frameworks like STRIDE or PASTA.
- Risk Assessment and Prioritization: Calculating risk using qualitative and quantitative methods, determining risk tolerance, and prioritizing threats based on likelihood and impact.
- Mitigation Strategy Development: Designing and implementing effective mitigation strategies, including preventative, detective, and corrective controls. This includes understanding the importance of layered security.
- Vulnerability Management: Identifying and assessing system vulnerabilities, prioritizing remediation efforts based on risk, and leveraging vulnerability scanning tools.
- Incident Response Planning: Developing and practicing incident response plans, including communication protocols, escalation procedures, and post-incident analysis.
- Regulatory Compliance: Understanding relevant regulations and standards (e.g., NIST Cybersecurity Framework, ISO 27001) and ensuring compliance within mitigation plans.
- Communication and Collaboration: Effectively communicating risk assessments and mitigation strategies to technical and non-technical audiences; collaborating with stakeholders across different departments.
- Practical Application: Be prepared to discuss real-world scenarios and how you would apply your knowledge to assess and mitigate specific threats. Consider examples from your past experience.
- Problem-Solving Approaches: Showcase your ability to think critically, analyze complex situations, and propose effective solutions under pressure. Be ready to discuss your problem-solving methodology.
Next Steps
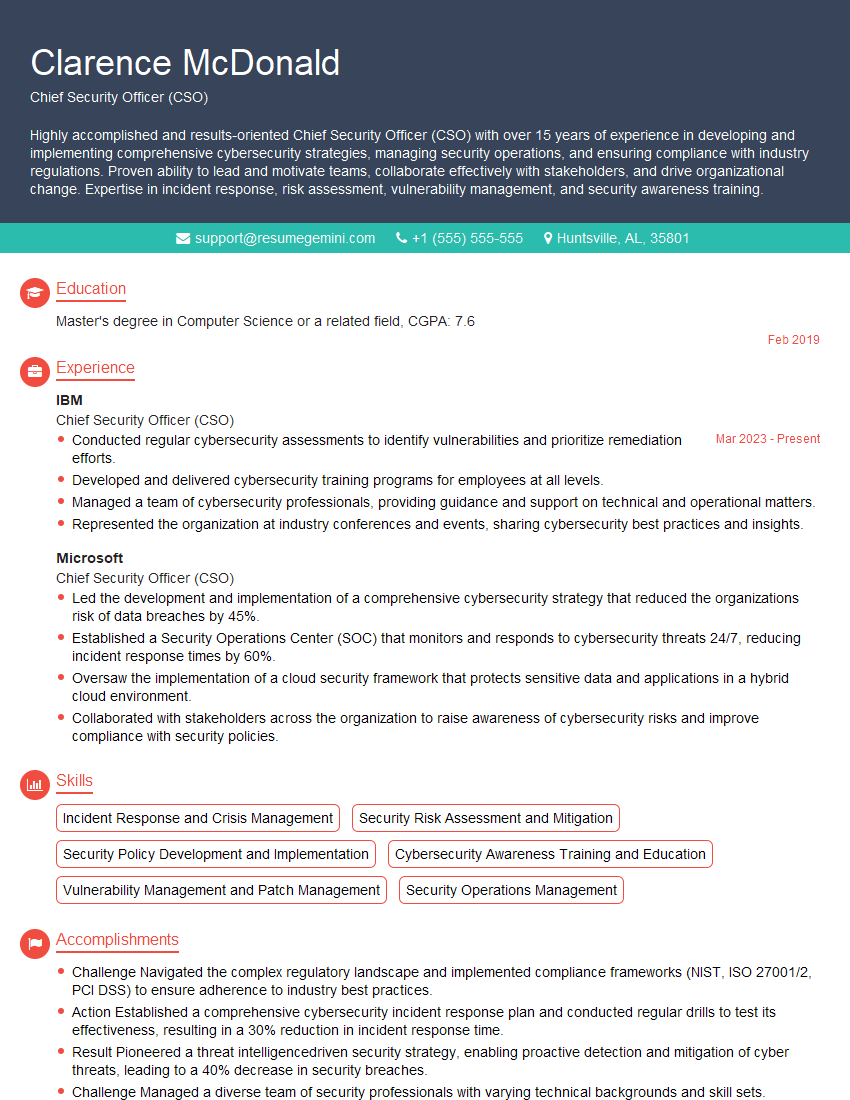
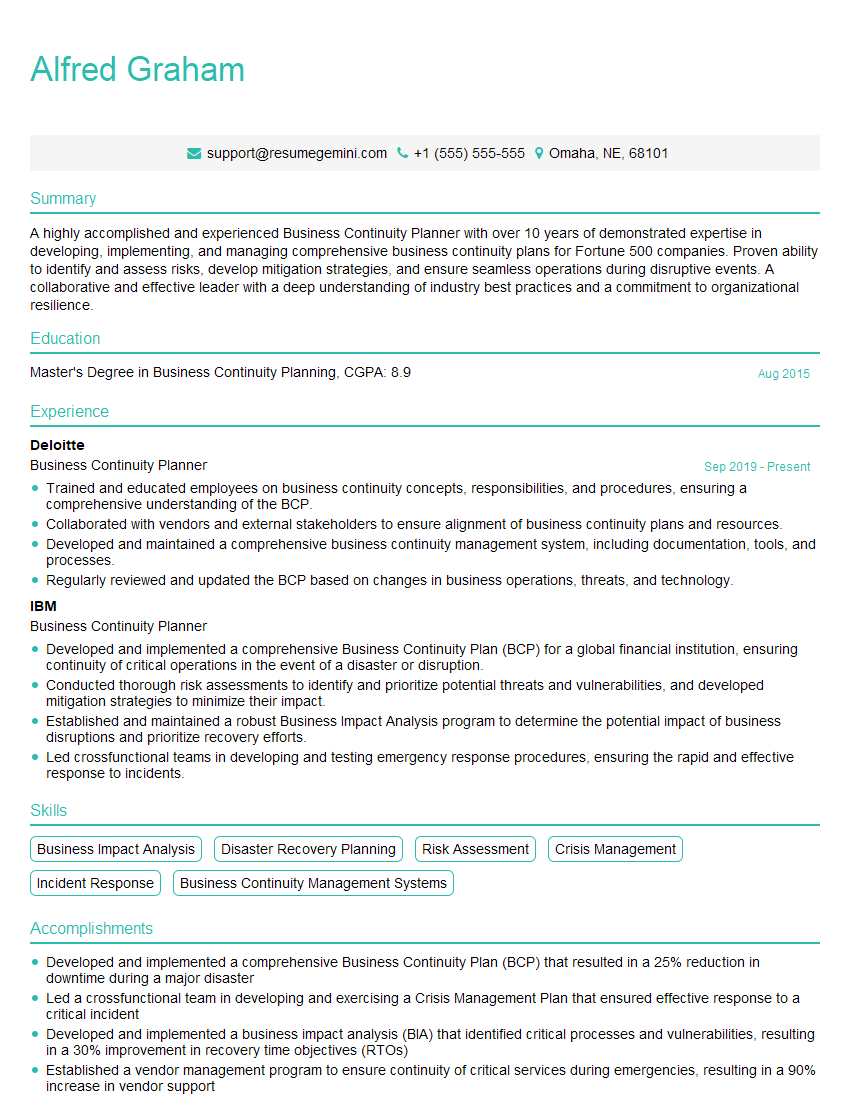
Mastering Threat Assessment and Mitigation Planning is crucial for career advancement in cybersecurity and related fields. It demonstrates a critical skillset highly sought after by employers. To maximize your job prospects, focus on building a strong, ATS-friendly resume that highlights your expertise. ResumeGemini is a trusted resource to help you craft a professional and impactful resume that showcases your skills and experience effectively. Examples of resumes tailored to Threat Assessment and Mitigation Planning are available, allowing you to leverage best practices and present your qualifications in the most compelling way.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
To the interviewgemini.com Webmaster.
Very helpful and content specific questions to help prepare me for my interview!
Thank you
To the interviewgemini.com Webmaster.
This was kind of a unique content I found around the specialized skills. Very helpful questions and good detailed answers.
Very Helpful blog, thank you Interviewgemini team.