The thought of an interview can be nerve-wracking, but the right preparation can make all the difference. Explore this comprehensive guide to Experience in working with wireless communication systems interview questions and gain the confidence you need to showcase your abilities and secure the role.
Questions Asked in Experience in working with wireless communication systems Interview
Q 1. Explain the difference between OFDM and OFDMA.
Both OFDM (Orthogonal Frequency Division Multiplexing) and OFDMA (Orthogonal Frequency Division Multiple Access) are modulation techniques that divide a wide communication channel into many narrowband subcarriers, transmitting data simultaneously across them. Think of it like sending many smaller packages instead of one large one – more efficient and robust against interference. The key difference lies in how they manage these subcarriers. OFDM uses all subcarriers for a single user, while OFDMA allows the system to allocate different subsets of subcarriers to multiple users at the same time.
Imagine a highway (the communication channel). OFDM is like a single car using all the lanes, while OFDMA is like multiple cars using different combinations of lanes simultaneously, increasing overall capacity and efficiency. This makes OFDMA particularly useful in high-density environments, such as crowded urban areas, where many devices compete for the same wireless spectrum.
- OFDM: One user, all subcarriers.
- OFDMA: Multiple users, different subsets of subcarriers.
Q 2. Describe the various types of wireless channel impairments.
Wireless channels are notoriously unpredictable. Several impairments can significantly affect the quality of communication. These include:
- Path Loss: Signal strength weakens with distance from the transmitter. It’s like a lightbulb – the further you are, the dimmer it appears.
- Multipath Propagation: Signals can bounce off objects, arriving at the receiver via multiple paths with different delays. This can cause constructive and destructive interference, leading to fading.
- Shadowing: Obstacles like buildings or trees block the signal, causing significant attenuation. It’s like someone standing in front of your lightbulb.
- Doppler Shift: Relative motion between the transmitter and receiver causes a change in the signal frequency. This is akin to the change in pitch of an ambulance siren as it passes by.
- Noise: Unwanted signals from various sources (thermal noise, atmospheric noise, etc.) interfere with the transmitted signal. This is like background static on a radio.
- Interference: Signals from other transmitters operating on the same or adjacent frequencies can overlap and disrupt the communication.
Understanding and mitigating these impairments is crucial for designing robust wireless systems.
Q 3. What are the advantages and disadvantages of different multiple access techniques (e.g., TDMA, FDMA, CDMA)?
Multiple Access Techniques (MATs) determine how multiple users share the available bandwidth and time resources. Each has its own set of advantages and disadvantages:
- TDMA (Time Division Multiple Access): Users are allocated different time slots within a frequency channel. Think of it like taking turns speaking in a conversation.
- FDMA (Frequency Division Multiple Access): Users are allocated different frequency bands. It’s like having separate radio channels for each user.
- CDMA (Code Division Multiple Access): Users share the same frequency band, but are distinguished by unique codes. This is like having multiple conversations happening simultaneously in the same room, each using a different language.
TDMA Advantages: Simple to implement; good for low data rate applications. Disadvantages: Low spectral efficiency; sensitive to synchronization errors.
FDMA Advantages: Relatively simple; good for voice communication. Disadvantages: Requires precise frequency allocation; inflexible to changing traffic demands.
CDMA Advantages: High spectral efficiency; resistant to interference and fading. Disadvantages: Complex implementation; requires sophisticated signal processing.
The choice of MAT depends on factors such as the application’s bandwidth requirements, the number of users, and the desired level of robustness.
Q 4. Explain the concept of MIMO and its benefits in wireless communication.
MIMO (Multiple-Input Multiple-Output) technology employs multiple antennas at both the transmitter and receiver. This allows for spatial multiplexing, where multiple data streams are transmitted simultaneously over the same frequency band, significantly increasing data rates and improving link reliability.
Imagine throwing multiple balls simultaneously at different angles, reaching different targets (receivers). Each ball (data stream) travels independently and reaches its target without colliding with other balls, increasing the overall efficiency.
Benefits of MIMO:
- Increased Data Rates: Spatial multiplexing allows higher throughput.
- Improved Reliability: Diversity techniques using multiple antennas mitigate the effects of fading and interference.
- Extended Coverage: Beamforming capabilities enhance signal strength in desired directions.
MIMO is a cornerstone of modern wireless communication systems, enhancing the performance of Wi-Fi, 4G, and 5G networks.
Q 5. Describe the different layers of the OSI model relevant to wireless communication.
The OSI (Open Systems Interconnection) model is a conceptual framework for network communication. While the entire model applies to wireless communication, some layers are particularly relevant:
- Physical Layer: Deals with the physical transmission of bits over the wireless medium, including antenna characteristics, modulation techniques, and signal propagation.
- Data Link Layer: Provides error-free transmission of frames between two directly connected nodes, including MAC (Medium Access Control) protocols for channel access.
- Network Layer: Handles routing and addressing of packets across the network, determining the path data takes to its destination.
- Transport Layer: Ensures reliable and ordered delivery of data segments, including error detection and correction, flow control, and segmentation/reassembly.
Understanding these layers is essential for analyzing and troubleshooting wireless communication problems. For example, problems related to signal strength or interference often reside in the physical layer, whereas routing issues typically fall under the network layer.
Q 6. How does beamforming work in 5G networks?
In 5G networks, beamforming uses phased antenna arrays to focus the transmitted signal towards the intended receiver. By precisely adjusting the phase and amplitude of signals emitted from multiple antennas, the base station can create a narrow, directional beam that concentrates power in a specific direction. This significantly improves signal quality, extends coverage, and enhances spectral efficiency.
Imagine a spotlight – unlike a regular lightbulb which illuminates a wide area, a spotlight concentrates the light in a narrow beam. Similarly, beamforming concentrates the radio signal to the user, minimizing interference and enhancing signal strength.
Advanced algorithms in 5G base stations dynamically adjust the beam direction and shape based on the user’s location and channel conditions, further optimizing the performance.
Q 7. Explain the concept of network slicing in 5G.
Network slicing in 5G allows for the creation of multiple virtual networks on top of a shared physical infrastructure. Each slice is tailored to meet the specific requirements of different applications or services, such as high-bandwidth video streaming, low-latency autonomous driving, or massive IoT connectivity. Think of it like slicing a pizza – you can have different toppings (services) on each slice (network), all served from the same pizza (physical infrastructure).
This offers several advantages: improved resource utilization, enhanced Quality of Service (QoS) for specific applications, flexibility and scalability for diverse services, and increased security through isolation between slices.
For instance, a network slice for autonomous driving might prioritize ultra-low latency and high reliability, while another slice for IoT devices might prioritize massive connectivity and low power consumption. This allows for optimized resource allocation and tailored performance for diverse use cases within the same 5G network.
Q 8. What are the key performance indicators (KPIs) for a wireless network?
Key Performance Indicators (KPIs) for a wireless network are crucial metrics that measure its effectiveness and efficiency. They allow us to assess the network’s health, identify areas for improvement, and ensure a positive user experience. These KPIs can be broadly categorized into several key areas:
- Throughput/Data Rate: This measures the amount of data successfully transmitted per unit of time (e.g., Mbps). A higher throughput indicates a faster network. We monitor this closely to ensure applications perform as expected.
- Latency: This refers to the delay in data transmission between the sender and receiver. Lower latency is crucial for real-time applications like video conferencing or online gaming. High latency often points to network congestion or other issues.
- Packet Loss: This represents the percentage of data packets that are lost during transmission. High packet loss leads to dropped calls, interruptions in streaming services, and data corruption. Its causes can be diverse, ranging from interference to faulty hardware.
- Signal Strength/RSSI (Received Signal Strength Indicator): A crucial measure of the power level of a received wireless signal. Weak signals lead to reduced throughput and increased error rates. This is often displayed in dBm.
- Availability/Uptime: This represents the percentage of time the network is operational and accessible. High availability is paramount for mission-critical applications and services. We might monitor this via network monitoring tools.
- Error Rate (BER/PER): Bit Error Rate (BER) or Packet Error Rate (PER) measures the frequency of errors in data transmission. High error rates significantly impact data reliability.
- Jitter: This measures the variation in latency, which can affect real-time applications like VoIP. High jitter can lead to choppy audio or video.
By consistently monitoring these KPIs and analyzing trends, we can proactively identify and address network issues before they impact users. For instance, a sudden drop in throughput might indicate an overloaded network, while high latency could signify a problem with routing or congestion. We’d use these insights to optimize network settings, upgrade hardware, or improve network design.
Q 9. Describe your experience with wireless protocol testing and debugging.
My experience with wireless protocol testing and debugging spans several years and diverse technologies. I’ve extensively used protocol analyzers like Wireshark and tcpdump to capture and analyze network traffic. This helps in identifying specific protocol violations, errors, and performance bottlenecks. For instance, I once used Wireshark to pinpoint an issue with a specific implementation of the 802.11ac protocol where packets were experiencing higher than average latency due to incorrect frame aggregation settings.
My debugging approach is systematic. It usually involves:
- Identifying the symptoms: Clearly defining the problem, such as slow speeds, connectivity drops, or specific application failures.
- Gathering information: Using tools to collect data, including signal strength readings, error rates, and network traffic captures.
- Isolating the cause: Analyzing the collected data to pinpoint the root cause of the issue. This might involve examining logs, configurations, and hardware.
- Implementing a solution: Implementing the necessary changes to resolve the problem. This could range from simple configuration adjustments to more complex hardware or software upgrades.
- Verification and testing: Rigorously testing the solution to ensure its effectiveness and stability.
I’m proficient in testing various protocols, including 802.11 (a/b/g/n/ac/ax), Bluetooth, and Zigbee. I have experience with both manual and automated testing procedures, using tools like Ixia and Spirent for load testing and performance analysis. I also have experience with scripting (Python, TCL) to automate repetitive testing tasks and generate detailed reports.
Q 10. How do you troubleshoot connectivity issues in a wireless network?
Troubleshooting connectivity issues in a wireless network involves a methodical approach. It begins with identifying the affected devices and symptoms. The steps I usually follow include:
- Verify the basics: Check if the wireless adapter is enabled on the affected devices, and ensure the correct SSID and password are used. Confirm the router is powered on and broadcasting the signal.
- Check signal strength: Use a signal strength meter on the affected device or a network survey tool to determine the strength and quality of the Wi-Fi signal. Weak signals are a common cause of connectivity problems.
- Examine the router configuration: Check the router’s settings for any issues like incorrect channel selection, disabled wireless features, or firewall rules that might be blocking access.
- Check for interference: Identify potential sources of interference, such as other wireless devices (microwaves, cordless phones), physical obstructions (walls, furniture), or adjacent Wi-Fi networks operating on the same channel. Using a wireless analyzer can help here.
- Check for driver or firmware issues: Update the wireless network adapter drivers on the affected devices and check if the router’s firmware is up-to-date.
- Perform a ping test: Use the
pingcommand to check connectivity to the router’s IP address or other known network resources. Successful pings indicate basic network connectivity. - Check network logs: Examine the router’s logs for any error messages or warnings that might provide clues about the cause of the problem.
- Reboot the devices: Restart both the router and the affected devices. Often, a simple reboot can resolve temporary glitches.
If the problem persists, more advanced troubleshooting techniques may be necessary. This might involve checking network cabling, analyzing network traffic, or employing packet capture and analysis tools to diagnose deeper issues.
Q 11. Explain your understanding of different modulation schemes (e.g., QAM, PSK).
Modulation schemes are methods used to encode digital data onto an analog carrier signal for transmission in wireless systems. They determine how efficiently data is transmitted and how resistant the signal is to noise and interference. Here’s a description of some common modulation schemes:
- Quadrature Amplitude Modulation (QAM): This scheme uses both amplitude and phase changes to represent data. Higher-order QAM (e.g., 64-QAM, 256-QAM) can transmit more bits per symbol, resulting in higher data rates. However, it is more susceptible to noise and interference. It’s often used in high-speed data applications like cable internet and DSL.
- Phase-Shift Keying (PSK): This scheme uses phase changes to represent data. Different PSK variations (e.g., BPSK, QPSK, 8PSK) offer varying data rates and noise immunity. BPSK is robust but slower; higher-order PSK achieves higher data rates but is less resistant to noise.
The choice of modulation scheme depends on various factors, including the desired data rate, the available signal-to-noise ratio (SNR), and the required level of error correction. For instance, in environments with high interference, a robust but lower-throughput scheme like BPSK might be preferred, while in a cleaner environment, a higher-order QAM could be used to achieve higher data rates. Understanding these trade-offs is critical in designing and optimizing wireless systems.
Q 12. What are the challenges of deploying wireless networks in rural areas?
Deploying wireless networks in rural areas presents unique challenges compared to urban settings. These challenges primarily stem from the characteristics of rural environments:
- Geographic Dispersion: Rural areas often have widely scattered populations, requiring a much larger coverage area and potentially necessitating the use of more powerful transmitters and a greater number of access points or base stations to provide reliable connectivity.
- Terrain Obstacles: Hills, mountains, and forests can significantly attenuate the wireless signal, leading to reduced range and signal strength. Line-of-sight is crucial for optimal performance.
- Limited Infrastructure: Rural areas often have limited or nonexistent existing infrastructure, such as power grids and fiber optic cables, making it more challenging and expensive to deploy and maintain the network infrastructure.
- Lower Population Density: The lower population density reduces the economic viability of deploying a high-capacity network, as the cost per user may be significantly higher.
- Environmental Factors: Severe weather conditions, such as storms and heavy snowfall, can severely impact wireless network performance and reliability.
- Cost of Deployment: Deployment costs are higher in rural areas due to geographical factors and the need for extended infrastructure.
To overcome these challenges, solutions often involve using specialized technologies like directional antennas, mesh networks, and satellite communication to extend coverage and improve reliability. Careful site surveys and network planning are essential to ensure optimal coverage and minimize interference.
Q 13. Describe your experience with different wireless technologies (e.g., Wi-Fi, Bluetooth, Zigbee).
My experience encompasses a broad range of wireless technologies, including Wi-Fi, Bluetooth, and Zigbee. Each technology has its strengths and weaknesses, making it suitable for different applications:
- Wi-Fi (IEEE 802.11): Provides high-speed data transmission over relatively long ranges. I have extensive experience with various Wi-Fi standards (a, b, g, n, ac, ax), including configuring access points, optimizing network performance, and troubleshooting connectivity issues. Wi-Fi is ideal for applications like internet access, local area networking, and streaming media.
- Bluetooth: A short-range wireless technology primarily used for connecting personal devices. I have experience with classic Bluetooth and Bluetooth Low Energy (BLE), working on projects involving device pairing, data transfer, and integration with various applications. Bluetooth is suitable for applications like audio streaming, proximity sensing, and wearable device connectivity.
- Zigbee: A low-power, low-data-rate wireless technology designed for mesh networking. I’ve worked with Zigbee for applications requiring long battery life and robust mesh networking capabilities. Zigbee is often used in smart home automation, industrial monitoring, and sensor networks.
My experience with these technologies goes beyond basic implementation. I understand the nuances of their respective protocols, including their strengths, limitations, and security considerations. This holistic understanding helps me to choose the optimal technology for each specific application and design reliable and efficient wireless systems.
Q 14. How do you ensure security in a wireless network?
Ensuring security in a wireless network is paramount. It’s a multi-layered approach that combines technical measures and security policies. Here are some key strategies I employ:
- Strong Passwords/WPA3/WPA2 Encryption: Using strong, unique passwords and implementing robust encryption protocols like WPA3 (or WPA2 as a fallback) is essential to prevent unauthorized access to the network. WPA3 offers improved security compared to its predecessor.
- MAC Address Filtering: This feature allows restricting access to the network only to devices with specific MAC addresses, enhancing security by blocking unwanted connections.
- Firewall Configuration: Configuring a firewall on the router to block unauthorized access attempts and malicious traffic is crucial for network security. This can involve setting up rules to block specific ports and IP addresses.
- Regular Firmware Updates: Keeping the router’s firmware up-to-date is essential to patch known security vulnerabilities. Manufacturers regularly release updates to address security flaws.
- Virtual Private Networks (VPNs): For increased security when using public Wi-Fi, VPNs encrypt network traffic, protecting data from eavesdropping and interception.
- Network Segmentation: Dividing the network into multiple smaller segments can limit the impact of security breaches. If one segment is compromised, it doesn’t necessarily compromise the entire network.
- Regular Security Audits: Performing regular security audits helps to identify vulnerabilities and ensure that security measures are effective. This could include penetration testing.
- User Education: Educating users about safe internet practices, such as avoiding suspicious websites and strong password creation, is an often overlooked but crucial aspect of network security.
Implementing a combination of these strategies provides a multi-layered defense against various threats, ensuring the confidentiality, integrity, and availability of the network and the data it carries.
Q 15. Explain the concept of handover in cellular networks.
Handover, also known as handoff, is a crucial process in cellular networks that ensures continuous connectivity for a mobile user as they move from one base station’s coverage area to another. Think of it like seamlessly switching between different radio stations in your car as you drive – you don’t experience any interruption in the music. In cellular networks, this seamless transition is vital for maintaining call quality and data transmission.
The process involves several steps: First, the network monitors the signal strength of the current base station and neighboring base stations. When the signal strength from the current base station drops below a certain threshold, or the signal from a neighboring base station becomes stronger, the network initiates a handover. This involves negotiating the connection with the new base station and transferring the call or data session. Several handover strategies exist, including hard handoffs (a complete break before connecting to the new base station) and soft handoffs (connecting to the new base station before disconnecting from the old one), with soft handoffs being preferred for their improved quality and reduced call drops.
Effective handover management is crucial for a good user experience. Poor handover can lead to dropped calls, data interruptions, and latency issues. This is why network operators constantly monitor and optimize their handover procedures.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is the difference between FDD and TDD in cellular networks?
FDD (Frequency Division Duplex) and TDD (Time Division Duplex) are two different methods for allocating the radio frequency spectrum in cellular networks. They differ fundamentally in how they separate the uplink (mobile device to base station) and downlink (base station to mobile device) communication channels.
- FDD: In FDD, separate frequency bands are used for the uplink and downlink. Imagine a two-lane highway: one lane for traffic going one way (uplink), and another for the opposite direction (downlink). This allows for simultaneous transmission and reception, potentially offering higher throughput. However, it requires twice the amount of spectrum compared to TDD.
- TDD: In TDD, the same frequency band is used for both uplink and downlink communication, but at different times. Think of a single lane highway where traffic flows in one direction for a certain period and then switches to the opposite direction. The time allocation for uplink and downlink can be dynamically adjusted depending on the traffic demands. This is particularly useful in situations where uplink or downlink traffic is significantly higher.
The choice between FDD and TDD depends on various factors, including spectrum availability, traffic patterns, and the specific needs of the network. For instance, TDD is often preferred in networks with highly fluctuating traffic demands or where spectrum is scarce, whereas FDD is generally favored where high symmetrical data throughput is consistently required.
Q 17. Describe your experience with wireless network planning and optimization tools.
Throughout my career, I’ve extensively used various wireless network planning and optimization tools. My experience includes working with both commercial and open-source solutions. For example, I’ve used Atoll Network Planner for detailed macro-cell network design, considering terrain, building penetration losses, and other environmental factors to predict coverage and signal strength. I’ve also utilized TEMS Pocket for drive testing and post-processing of collected data to identify coverage holes, interference issues, and optimize cell parameters. In addition, I’ve worked with network optimization platforms, leveraging machine learning algorithms to predict network performance and identify areas for improvement.
These tools allow for detailed network simulations, helping to predict performance before deploying new infrastructure. I’ve used this to minimize capital expenditures and maximize the effectiveness of network deployments. Moreover, my experience with these tools extends to analyzing network performance data to pinpoint areas requiring adjustments or upgrades, thus ensuring optimal network performance and user experience.
Q 18. Explain your understanding of different antenna types and their applications.
Antenna types play a critical role in wireless communication, shaping the radiation pattern and efficiency of signal transmission and reception. The choice of antenna depends heavily on the application and environmental factors.
- Omni-directional antennas: These radiate signals equally in all horizontal directions, making them suitable for providing broad coverage, like in cellular base stations covering large areas. They are relatively simple and cost-effective.
- Directional antennas: These focus the signal in a specific direction, maximizing signal strength in that direction while minimizing interference in others. These are commonly used in point-to-point links or in situations where precise beamforming is required, such as in microwave backhaul links.
- Parabolic antennas: These are highly directional antennas with a parabolic reflector that focuses the radio waves into a narrow beam. Their high gain and directivity make them ideal for long-distance communication, like in satellite communication or high-capacity point-to-point links.
- MIMO antennas: Multiple-Input and Multiple-Output (MIMO) antennas utilize multiple antennas at both the transmitter and receiver to improve data rates and link reliability by employing spatial multiplexing techniques.
In my work, I’ve selected antennas based on factors such as coverage requirements, signal strength needed, interference levels, and cost constraints. For instance, in a dense urban environment, I might choose directional antennas to mitigate interference, while in a rural area, omni-directional antennas might be more suitable to achieve broad coverage.
Q 19. How do you measure signal strength and quality in a wireless network?
Measuring signal strength and quality in a wireless network is essential for troubleshooting and optimization. This involves both drive testing and stationary measurements using specialized equipment.
Drive testing involves using a mobile device equipped with a signal analyzer to measure signal strength (usually in dBm), signal-to-noise ratio (SNR), and other key parameters while driving or walking through the coverage area. This provides a comprehensive overview of the network’s performance in various locations. Specialized drive test software is then used to analyze the collected data, visualizing coverage maps and identifying areas with weak signals or high interference.
Stationary measurements can be performed using a spectrum analyzer or a network analyzer, which provides more detailed information on frequency characteristics, interference sources, and signal quality. These measurements are useful for identifying specific interference sources and verifying the antenna performance.
In addition to specialized equipment, mobile network operators use sophisticated monitoring systems that track network performance indicators in real-time, providing crucial data for ongoing optimization and proactive problem resolution. These systems continuously monitor various parameters and automatically alert operators to potential issues.
Q 20. What is the role of a base station in a cellular network?
In a cellular network, the base station (often called a cell site or base transceiver station – BTS) serves as the central communication point between the mobile devices and the core network. It’s essentially the ‘radio hub’ for a specific geographical area (a cell).
Its key functions include:
- Radio transmission and reception: The base station transmits and receives radio signals to and from mobile devices within its coverage area.
- Frequency management: It manages radio frequency channels within its cell to ensure efficient and interference-free communication.
- Handoff management: It participates in the handover process, seamlessly transferring calls and data sessions to neighboring base stations as mobile devices move.
- Power control: It adjusts the transmission power of its radio signals to maintain optimal signal strength while minimizing interference and conserving energy.
- Data routing: It routes data traffic between mobile devices and the core network.
In essence, the base station is the critical link that connects mobile users to the broader cellular network, providing the necessary radio access and enabling communication.
Q 21. Explain your understanding of power control in wireless communication.
Power control is a fundamental aspect of wireless communication, aiming to optimize the use of transmitted power while ensuring reliable communication and minimizing interference. It’s a complex process involving various techniques and considerations.
The primary goals of power control are:
- Maximize battery life of mobile devices: By reducing the transmission power of mobile devices when possible, battery consumption is significantly reduced.
- Minimize interference: Reducing the transmission power of mobile devices prevents them from interfering with other nearby users or cells.
- Maintain sufficient signal strength: Power control ensures that the signal strength remains above a threshold to maintain reliable communication.
- Improve overall network capacity: Efficient power control can increase the overall capacity of the cellular network by allowing more users to be served simultaneously.
Power control mechanisms typically involve closed-loop control where the base station monitors the signal quality from mobile devices and adjusts their transmission power accordingly. Open-loop control involves pre-defined power levels based on the distance from the base station or other factors. Various algorithms are used to dynamically adjust power levels, balancing these competing objectives. Effective power control is crucial for efficient and reliable wireless communication networks, and its implementation often involves sophisticated signal processing and optimization techniques.
Q 22. Describe your experience with different wireless spectrum bands.
My experience spans several wireless spectrum bands, each with unique characteristics influencing data rate, range, and application suitability. I’ve worked extensively with:
- 2.4 GHz ISM band: This unlicensed band is ubiquitous, used in Wi-Fi, Bluetooth, and many IoT devices. Its advantages are widespread availability and low cost, but it suffers from congestion and interference, leading to lower data rates and reliability compared to licensed bands. For example, I worked on a project optimizing Wi-Fi performance in a densely populated office environment by strategically placing access points to minimize overlapping signals and interference.
- 5 GHz ISM band: Offering wider channels and less congestion than 2.4 GHz, it’s ideal for high-bandwidth applications like high-definition video streaming and fast data transfer. However, it has shorter range and can be more susceptible to signal attenuation by obstacles. In a recent project, I leveraged the 5 GHz band to deploy a high-speed wireless network for a manufacturing facility, balancing speed with sufficient coverage.
- Licensed bands (e.g., Cellular bands): These bands, like those used by 4G LTE and 5G, provide superior performance, reliability, and higher data rates due to dedicated frequency allocation and advanced signal processing techniques. However, they require licenses and are generally more expensive. I have experience in designing cellular-based IoT solutions, optimizing antenna placement and network configuration to ensure reliable communication in challenging environments.
Understanding the trade-offs between these bands is crucial for selecting the optimal technology for a specific application. Each project requires careful consideration of factors like cost, required data rate, coverage area, and the presence of potential interference.
Q 23. What are the challenges of deploying IoT devices using wireless communication?
Deploying IoT devices using wireless communication presents several challenges:
- Power Consumption: IoT devices are often battery-powered, demanding energy-efficient communication protocols and hardware. This often means compromising on data rates or range.
- Scalability: Managing thousands or millions of devices simultaneously requires robust network architectures and efficient data handling capabilities. Network congestion and efficient resource management become critical concerns.
- Security: IoT devices are often vulnerable to cyberattacks due to limited processing power and security features. Secure communication protocols and robust authentication mechanisms are paramount.
- Interoperability: Different IoT devices may use different communication protocols, making integration and interoperability challenging. Standardization and protocol compatibility are crucial for seamless operation.
- Network Coverage and Reliability: Ensuring reliable communication in diverse environments (rural, urban, indoor) requires careful consideration of signal propagation, interference, and network infrastructure design. This is especially difficult in areas with limited or no cellular coverage.
Addressing these challenges often requires a multifaceted approach, carefully selecting appropriate hardware and software, implementing robust security measures, and designing scalable and efficient network architectures. For example, I’ve worked on projects using Low Power Wide Area Networks (LPWANs) like LoRaWAN to address the power consumption and scalability issues in large-scale deployments.
Q 24. Explain your experience with network simulation tools (e.g., NS-3, MATLAB).
I’m proficient in using network simulation tools such as NS-3 and MATLAB for designing, analyzing, and optimizing wireless communication systems. NS-3 allows for detailed modeling of network protocols and physical layer characteristics, enabling accurate performance evaluation under various scenarios. I used NS-3 to model and analyze the performance of a new MAC protocol for low-power wide area networks, evaluating its throughput and energy efficiency under different traffic loads and channel conditions.
MATLAB, on the other hand, is excellent for signal processing, channel modeling, and algorithm development. I’ve used it extensively for designing and evaluating channel equalization algorithms for high-speed wireless systems. For instance, I developed a channel equalization algorithm in MATLAB, simulating its performance in various fading channels and comparing it against existing algorithms.
My experience with these tools allows me to predict the performance of wireless systems before physical deployment, significantly reducing development costs and time-to-market. The combination of NS-3 and MATLAB provides a comprehensive approach to analyzing and optimizing wireless communication systems.
Q 25. How do you ensure the reliability and availability of a wireless network?
Ensuring reliability and availability of a wireless network involves a multi-pronged approach:
- Redundancy: Implementing redundant hardware components (e.g., multiple access points, switches, routers) and network paths ensures continued operation even in case of failures. This is akin to having backup generators for a building’s power supply.
- Diversity Techniques: Employing techniques like antenna diversity (multiple antennas) and frequency diversity (using different frequencies) mitigate the impact of signal fading and interference.
- Error Correction Codes: Using robust error correction codes helps to recover data lost due to channel impairments, improving reliability.
- Network Monitoring and Management: Continuous monitoring of network performance metrics (e.g., signal strength, packet loss, latency) allows for proactive identification and resolution of problems before they impact users.
- Load Balancing: Distributing traffic across multiple access points prevents congestion and ensures that no single point of failure overwhelms the network.
- Proper Site Survey and Planning: Careful planning of antenna placement, channel selection, and consideration of potential interference sources are crucial for maximizing network coverage and reliability.
In a recent project involving a critical infrastructure network, we implemented a comprehensive monitoring system with alerts for critical thresholds, proactive maintenance schedules, and redundant equipment to ensure 99.99% uptime.
Q 26. Describe your experience with different wireless security protocols (e.g., WPA2, WPA3).
My experience includes working with various wireless security protocols, including WPA2 and WPA3. WPA2 (Wi-Fi Protected Access 2) utilizes the Advanced Encryption Standard (AES) to encrypt data transmitted over a Wi-Fi network. While highly secure for its time, vulnerabilities have been discovered, highlighting the importance of regular updates and employing strong passwords.
WPA3 (Wi-Fi Protected Access 3) addresses some of WPA2’s weaknesses by introducing stronger security features, including Simultaneous Authentication of Equals (SAE), which provides more robust protection against dictionary attacks and improved encryption techniques. SAE replaces the older and less secure Pre-Shared Key (PSK) authentication method. I have actively contributed to securing wireless networks by migrating from WPA2 to WPA3, thereby enhancing the security posture against emerging threats.
Beyond WPA2 and WPA3, I am familiar with other relevant protocols used in cellular networks (e.g., TLS, DTLS) and other wireless communication systems. The choice of security protocol depends on the specific application and its security requirements.
Q 27. What are the future trends in wireless communication technologies?
The future of wireless communication is shaped by several key trends:
- 6G and Beyond: The next generation of wireless networks will deliver significantly higher data rates, lower latency, and enhanced reliability compared to 5G. This will enable new applications in areas like extended reality (XR), autonomous vehicles, and the Internet of Things (IoT).
- AI and Machine Learning (ML): AI and ML will play an increasingly important role in network optimization, resource management, and security. Intelligent networks will self-optimize and adapt to changing conditions, improving efficiency and reliability.
- Increased Spectrum Utilization: Efficient utilization of the available spectrum is crucial, leading to the exploration of new frequency bands and advanced spectrum sharing techniques.
- Integration of Wireless Technologies: The convergence of different wireless technologies (e.g., Wi-Fi, 5G, satellite) will create more flexible and robust networks.
- Edge Computing: Processing data closer to the source (edge devices) will reduce latency and bandwidth requirements, enabling new real-time applications.
- Increased Focus on Security: Advanced security measures will be crucial to protecting increasingly interconnected wireless networks from various threats.
These trends point towards a future where wireless networks are more intelligent, efficient, reliable, and secure, enabling a wide range of transformative applications across various industries.
Q 28. Explain your approach to solving a complex wireless network problem.
My approach to solving a complex wireless network problem follows a structured, systematic process:
- Problem Definition and Analysis: Thoroughly understand the problem by gathering information, identifying root causes, and defining clear objectives. This involves analyzing network performance metrics, user feedback, and technical specifications.
- Hypothesis Generation: Formulate potential solutions based on my experience and knowledge. This often involves identifying several possible causes and potential solutions.
- Testing and Validation: Design and conduct experiments to validate hypotheses, using simulation tools and/or real-world testing to evaluate the effectiveness of potential solutions. This may involve prototyping and experimentation.
- Solution Implementation: Implement the most effective solution, taking into account factors such as cost, feasibility, and maintainability.
- Monitoring and Evaluation: Monitor the implemented solution to assess its effectiveness and identify any unexpected issues. This involves continuous performance monitoring and analysis.
- Iteration and Refinement: Based on the monitoring results, refine and improve the solution to optimize its performance and address any remaining challenges.
This iterative process allows me to effectively address complex problems, learning from both successes and failures, constantly improving my problem-solving skills. For example, troubleshooting a persistent connectivity issue in a large wireless network involved careful analysis of network logs, a series of targeted tests, and iterative refinement of network settings, ultimately identifying a misconfigured firewall as the root cause.
Key Topics to Learn for Wireless Communication Systems Interviews
- Fundamental Concepts: Understanding signal propagation, modulation techniques (e.g., OFDM, FSK), channel coding, and error correction. Be prepared to discuss the trade-offs between different techniques.
- Wireless Standards: Familiarity with common wireless standards like Wi-Fi (802.11), Bluetooth, LTE, and 5G. Know their strengths, weaknesses, and typical applications.
- Network Architectures: Deep understanding of cellular network architectures (e.g., GSM, UMTS, 5G NR), including different layers and protocols (e.g., TCP/IP, MAC). Practice explaining how these components interact.
- Antenna Theory and Design: Basic knowledge of antenna principles, gain, directivity, and polarization. Be ready to discuss how antenna selection impacts system performance.
- Practical Applications: Be prepared to discuss specific projects or experiences involving wireless communication systems. Focus on your contributions, challenges faced, and solutions implemented.
- Troubleshooting and Problem-Solving: Prepare examples demonstrating your ability to diagnose and resolve issues in wireless communication systems. Highlight your analytical and problem-solving skills.
- Security Considerations: Understanding security protocols and vulnerabilities in wireless networks, such as encryption methods and authentication mechanisms.
- Emerging Technologies: Show awareness of current trends and advancements in wireless communication, such as IoT, mmWave technology, and satellite communication.
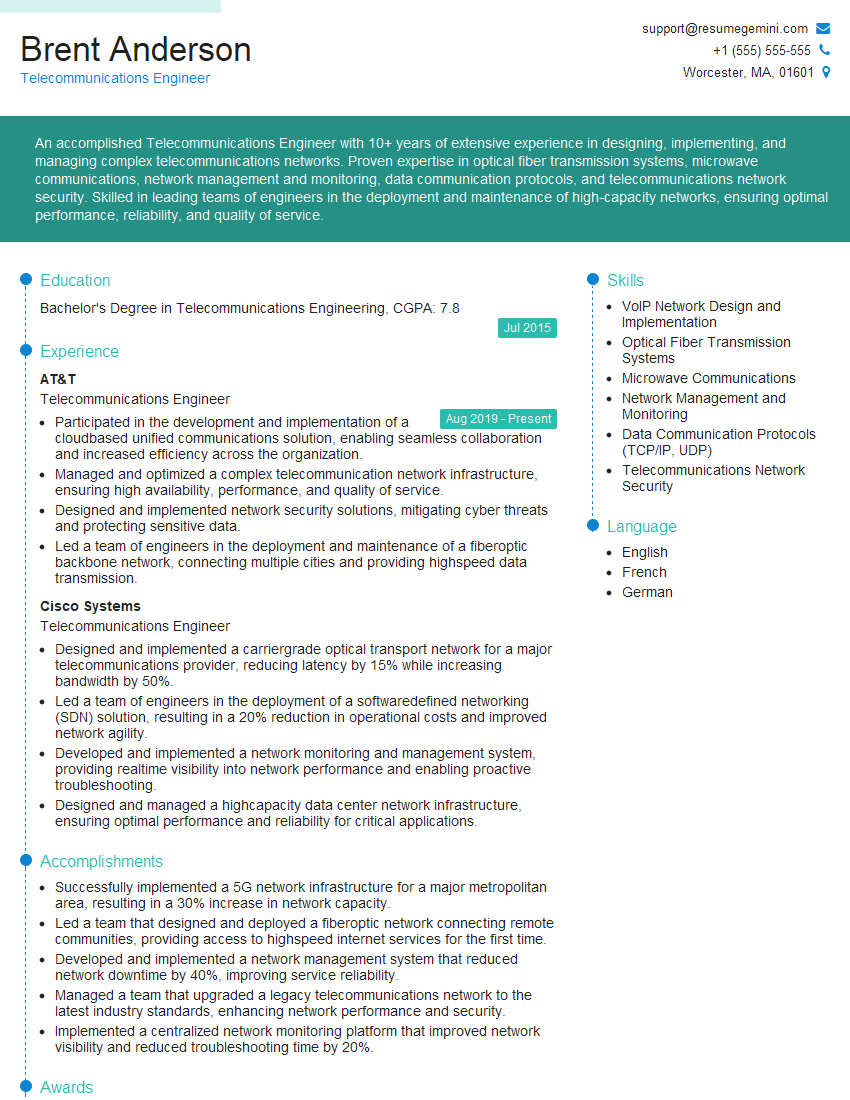
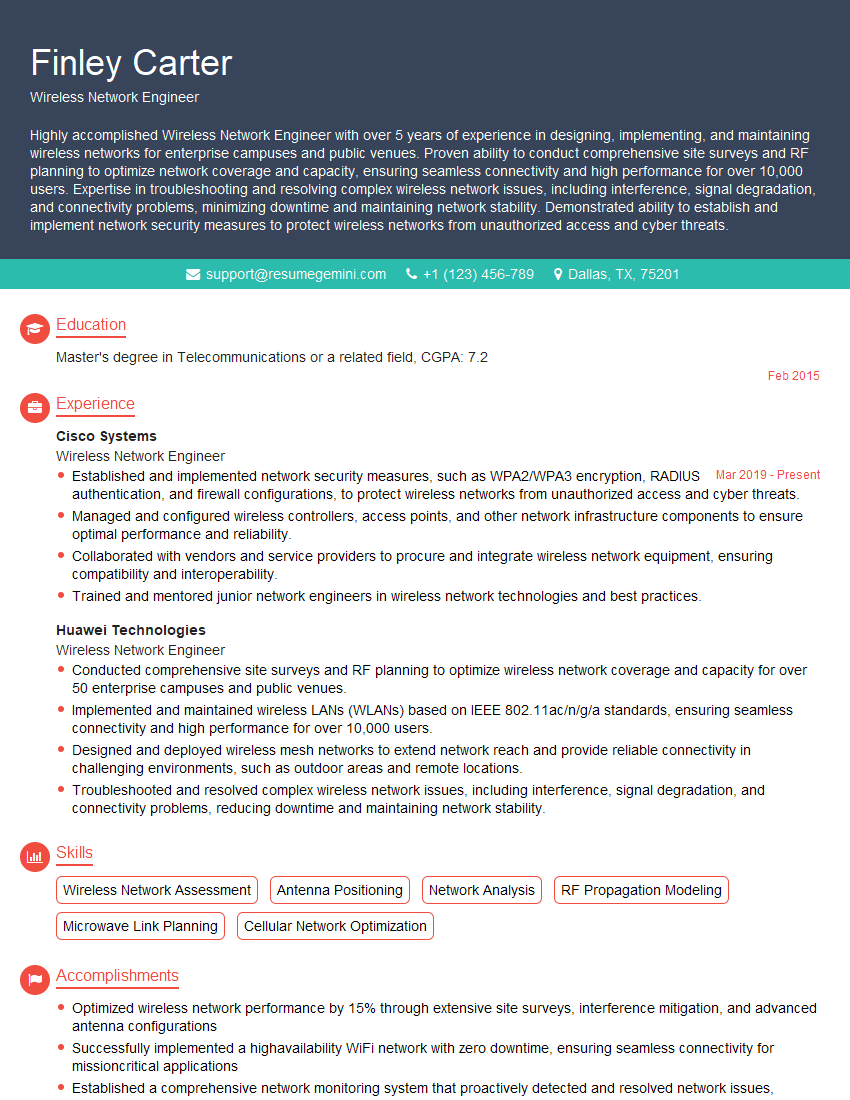
Next Steps
Mastering wireless communication systems knowledge significantly enhances your career prospects in a rapidly evolving technological landscape. It opens doors to exciting roles with high growth potential. To maximize your chances, create an ATS-friendly resume that highlights your skills and experience effectively. ResumeGemini is a trusted resource that can help you build a professional and impactful resume. We provide examples of resumes tailored to wireless communication systems experience to guide you in crafting your own compelling application. Use our resources to showcase your expertise and land your dream job!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
To the interviewgemini.com Webmaster.
Very helpful and content specific questions to help prepare me for my interview!
Thank you
To the interviewgemini.com Webmaster.
This was kind of a unique content I found around the specialized skills. Very helpful questions and good detailed answers.
Very Helpful blog, thank you Interviewgemini team.